April 12th, 2023 by Vladimir Katalov
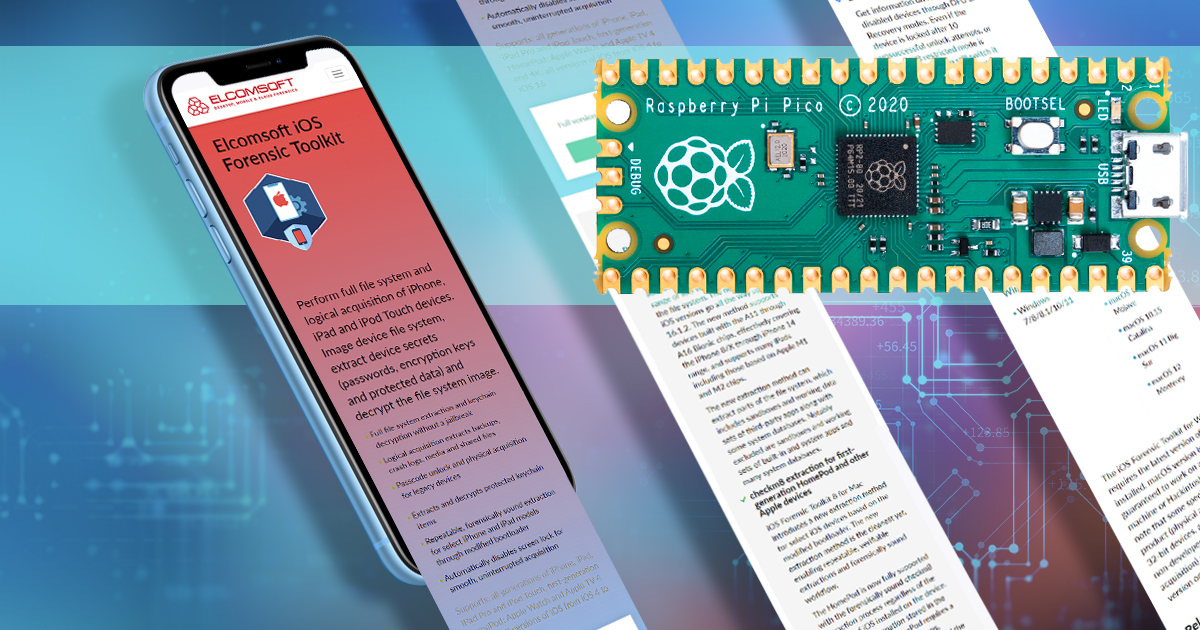
The latest update to iOS Forensic Toolkit brings two new features, both requiring the use of a Raspberry Pi Pico board. The first feature automates the switching of iPhone 8, iPhone 8 Plus, and iPhone X devices into DFU, while the second feature adds the ability to make long, scrollable screen shots in a semi-automatic fashion. In this article we will show how to build, program, and use a Raspberry Pi Pico board to automate DFU mode.
Read the rest of this entry »