Less than a month ago, we updated our Elcomsoft Phone Password Breaker tool with the ability to recover master passwords for BlackBerry Password Keeper and BlackBerry Wallet. I have blogged about that and promised the “next big thing” for BlackBerry forensics to be coming soon. The day arrived.
Today we are releasing a new version of Phone Password Breaker, this time adding the ability to recover security passwords protecting BlackBerry handsets. Yes, that is the very password used to lock and unlock the device. And yes, no one has done that before (well, at least not publicly).
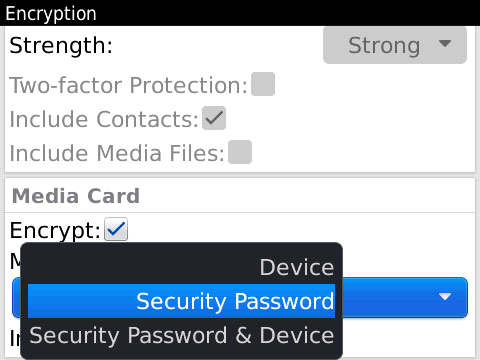
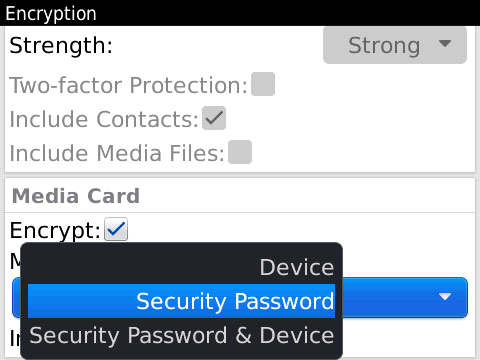
Before you get too excited, there is a catch. The new feature requires Media Card encryption to be switched on and set to either “Security Password” or “Device Password” mode. If this condition is met, EPPB will be able to run password recovery against device security password. What is also important and rather exciting is that you don’t need the BlackBerry device itself. All that is needed is a media card that was used in that device. Actually, we only need one specific file from that media card, so yes, the recovery can be off-loaded and the password can be recovered offline.
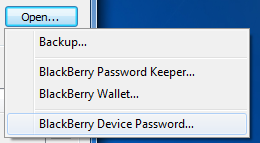
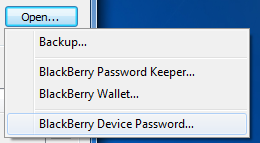
So how does this feature work? It’s pretty straightforward: launch Elcomsoft Phone Password Breaker, click Open and specify that you want to recover a BlackBerry security password. After that, you’ll need to navigate to the info.mkf file from the encrypted media card. It is located in BlackBerry/system directory on the media card, and is marked as hidden. Once you open the file (and only if the file comes from the card encrypted using the “Security Password” or “Device Password” option) you will be able to start the recovery as usual. The good news is that recovery rate is amazingly fast by today’s standards: it tries several million passwords per second on a modern multi-core CPU equipped with AES-NI instructions. With Intel i7-970, I am getting 1.8 million passwords per second in wordlist mode, and about 5.9 million passwords per second in bruteforce mode. Compare that to iPhone passcode recovery rate of less than six passcodes per second for iPhone 4, and try to think hard about BlackBerry having better security.
Among other changes in this version is preliminary support for iOS 5 backups. As Apple readies its newest and most advanced mobile OS yet, we have updated EPPB to make it compatible with backups produced by the latest beta of iOS 5. All the usual features (password recovery, backup decryption, and Keychain explorer) are available for iOS 5 backups.
Speaking of iOS backup decryption, we added another option demanded by our customers. EPPB can now recover original file names when decrypting a backup. That means you will get a directory structure and meaningful file names, making it easier to explore and analyze backup contents.
I really hope you will enjoy the new features.