As you may already know from our official announcement, we’ve recently updated Elcomsoft Phone Breaker to support Apple accounts upgraded to iCloud Drive and decrypting keychains from iCloud. Considering that one can access files stored in iCloud Drive without any third-party tools, is the update really worth the buzz? Read along to find out!
Before getting to the updated technology, let’s have a look at what Apple iCloud Drive is, and how it’s different from “classic” iCloud.
Apple iCloud
Back in 2011, Apple introduced a cloud storage system they called iCloud. The primary purpose of the cloud-based system was allowing users to automatically back up the content of their iOS devices over a Wi-Fi connection, and to restore those backups wirelessly onto a new device should the user lose or replace their old device. iOS 5 or later was required to use iCloud.
In addition to device backups, iCloud offered a platform for Apple and third-party application developers enabling to store and sync application data. Users could store documents, bookmarks, music, camera roll, calendar events, notes, e-books and other types of data.
However, there were major differences and severe limitations compared to “real” cloud storage services such as Dropbox, Box.com, Google Drive or Microsoft OneDrive. There was no way to access device backups stored in iCloud accounts other than restoring the backup onto a newly activated (or factory-reset) iOS device. There was no universal access to application data such as documents and music, too. One could only access these files from an iOS device via the application that originally saved the data.
iCloud Drive
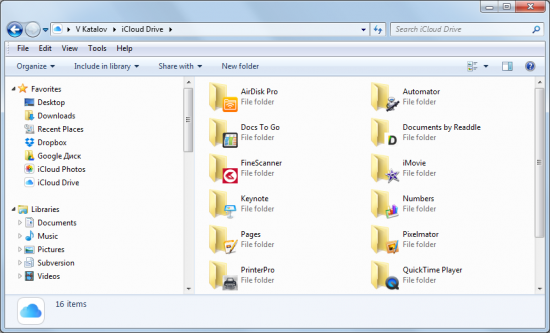
This was changed in 2014 with the release of iCloud Drive. With the release of iOS 8, Apple introduced the ability to store just about any type of data in the cloud. Clients for iOS 8, Windows 7 and later, and OS X Yosemite (10.10) were released, finally enabling access to cloud data from other platforms. In a way, iCloud Drive has become similar to other cloud storage providers… only it’s different.
It’s Different
With typical Apple’s attention to detail, using iCloud Drive is a joy. A client application simply adds a new drive letter that the user can simply copy all types of files to. That’s it, the sync is completely automatic.
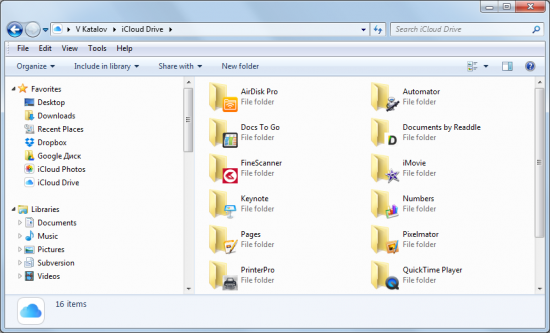
While users can store just about anything in iCloud Drive and use their Windows 7 or Mac OS X computers to access those files, some key areas still remain inaccessible via standard means. iOS backups and stored iOS app data are still stored separately, and Apple still provides no access to that data via any method other than restoring the backup to a new iOS device. There is still no direct access to iCloud files from iOS devices; only an API exists for app developers. This is a key difference between iCloud Drive and other cloud storage services that allow unconditional access to everything uploaded by the user.
As a result, a third-party tool is still needed if you want to download an iOS backup from an iCloud Drive account – just like it used to be with the classic iCloud.
Apple iCloud and iCloud Drive may look similar from the outside, but use different protocols under the hood. For this reason, upgrade to iCloud Drive is not automatic for those migrating to iOS 8. Instead, iOS users are offered to upgrade their iCloud accounts to iCloud Drive when activating a new iOS 8 device or upgrading to the latest version of iOS. Since there is no backward compatibility between iCloud Drive and iOS 7 and earlier, users with a mix of Apple hardware may wish to stay on classic iCloud until all of their iOS devices are running iOS 8.
The Solution
Finally we arrived to the point. Starting with this release, Elcomsoft Phone Breaker gains the ability to retrieve application data and user-loaded from user accounts upgraded to iCloud Drive – all that in addition to accessing iOS backups! While this is a short line of news, we spent nearly half a year reverse-engineering the new communication protocols and building code to communicate with iCloud Drive servers. We’ve finally succeeded, and it’s just in time.
Decrypting Keychain from iCloud Backups
It may sound confusing, but we are NOT decrypting iCloud Keychain. So what exactly DO we decrypt in this update? Before we go on to that, let’s have a look at these keychains first.
Keychain is a highly protected system database in iOS that keeps the most sensitive information stored in the device. Both system and third-party apps can use keychain to store protected data such as account passwords, payment information, Wi-Fi and VPN passwords, as well as various tokens and security certificates.
While stored in the device itself, the keychain is encrypted to the highest level available to the combination of hardware and software (iOS version) being used. However, once the keychain is extracted from the device and saved into a backup file, it may use a different protection level and encryption method altogether depending on the type of backup.
If the user creates a password-protected local backup with iTunes, the keychain is encrypted with a key dependent on the user-specified backup password. If you know the original backup password, you can decrypt MOST items stored in the keychain (by using the corresponding “Keychain Explorer” feature in Elcomsoft Phone Breaker).
If, however, a local backup is created without a password, the keychain will be extracted as-is (that is, encrypted with a hardware-dependent key that is unique to a particular device and does not change throughout the life of it). Now, these keychains can only be restored to the same physical device, and decrypted with the same hardware-dependent decryption key. However, if you do have that key (e.g. extracted via physical acquisition with Elcomsoft iOS Forensic Toolkit), you can decrypt ALL items from that keychain. Do note that there are numerous limitations as to which devices can or cannot be acquired via physical imaging.
Finally, if you have a cloud backup (iCloud), that backup will store the keychain protected with device password (similar to non-password-protected iTunes backups). While the encryption is mostly similar to that used in non-password-protected iTunes backups, some details are different. Therefore, decrypting the keychain extracted from an iCloud backup requires a slightly different approach.
Now when we know the theory, we can go on to the big news: Elcomsoft Phone Breaker can now decrypt all three types of keychains (provided that you have the hardware-dependent key, that is). If you want to decrypt the keychain extracted from an iCloud backup, you will need to extract the ‘securityd’ (0x835) key from the device via physical acquisition. You can just do it once, and the key can be used for decrypting all future iTunes and iCloud backups made from that device, even if the device will be factory-reset.
This is the Future
According to Apple, more than 72% of its users have already migrated to iOS 8, gaining the possibility to upgrade their iCloud service to iCloud Drive. However, there is no data available about how many users have actually switched their iCloud service to iCloud Drive. Still, since this is a one-way process (Apple provides no way of downgrading an iCloud Drive account to classic iCloud), we expect more users migrate to the new cloud storage.
Make sure to update your copy of Elcomsoft Phone Breaker to the latest release to be able to access the growing number of iCloud Drive accounts. Existing customers can download an update on its product page https://www.elcomsoft.com/epb.html .