We have just released a brand new tool, and this time it’s not about mobile forensics. Or is it?
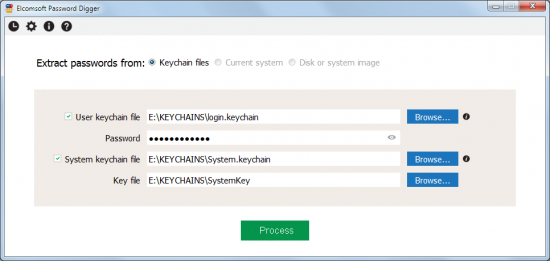
Elcomsoft Password Digger is designed for decrypting the content of Mac OS protected storage, the keychain. For one, it’s a Windows tool, so you’ll need to pull keychain files from the Mac OS system along with any decryption metadata (such as the key file for the system keychain or user’s password for decrypting the user keychain). After decrypting the keychain, we’ll export everything into an XML, and create a filtered plain-text file that only contains passwords (to be used as a pluggable dictionary in various password recovery tools).
So what is this all about?
Mac OS Keychain
It’s about passwords. This time around, we are targeting passwords Mac OS users keep in the Keychain. If you follow our blog, you’ve already head of iOS keychain. In iOS-powered devices such as iPhone and iPad, keychain is used to keep a lot of highly sensitive information. With every major iOS release, Apple seems to move more and more stuff under the umbrella of this encrypted storage.
Dealing with iOS keychains is extremely tough, as those are securely protected by strong, hardware-based encryption keys. When dealing with an iPhone, we can only access decrypted keychain via physical acquisition (jailbreak required, 32-bit devices only) or extract from a password-protected backup. Fortunately, keychain acquisition is much easier for computers running Apple’s desktop OS, Mac OS X.
According to various sources, approximately 4.9 to 6.5 of all desktop and laptop computers are running Mac OS X. The use of Mac OS is on the rise, with more Apple computers sold every year compared to other platforms. In Mac OS, the keychain plays the role of a system-wide, centralized password storage. It’s preinstalled on every system, it’s convenient and extremely simple to use, which makes it the tool of choice for most users. As a result, nearly every password a Mac OS user ever types ends up in the keychain.
What’s In There?
As already mentioned, nearly every password the user ever types ends up in the keychain. After just a few days of using the system, the user may’ve already typed the following passwords:
System Keychain
- Wi-Fi passwords
- User Keychain
- Apple ID password
- Password to iTunes backups
- AirPort and TimeCapsule passwords
- Passwords to Web sites and accounts
- VPN, RDP, FTP and SSH passwords
- Passwords to mail accounts including Gmail and Microsoft Exchange
- Passwords to social networks
- Passwords to network shares
- iWork document passwords
That’s a lot of passwords in a single storage! Extracting them can surely help an investigation. However, there is one particular password that can help the most. And that is the user’s Apple ID password.
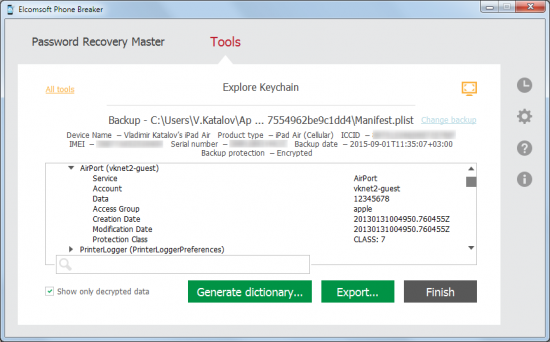
Apple ID Password: The Goldmine
If you manage to decrypt the keychain and discover the user’s Apple ID and password, you may have just found a goldmine. With Apple ID and password, you may be able to log in to the user’s Apple account to download and analyze over-the-air backups saved by all iOS devices registered to that account. This includes the user’s iPhone, iPad and iPod Touch devices. If you’re lucky and no two-factor authentication is present, you can simply use Elcomsoft Phone Breaker Forensic to download a clean, unencrypted backup that can be viewed in Elcomsoft Phone Viewer or analyzed in one of the many commercial forensic tools.
Building a Custom Dictionary
Another purpose of using Elcomsoft Password Digger is building a custom dictionary containing all of the user’s passwords. As you may know, many types of passwords are just too slow to brute force. For example, even if you use a high-end hardware accelerator, you can only try about 25,000 password combinations per second when attacking documents encrypted with Microsoft Office 2013. That’s not a lot, and rules out attacks on long, complex passwords – unless you have a good dictionary. And what could be more relevant for breaking a strong password than a dictionary containing that user’s other passwords? Elcomsoft Password Digger builds just that: a highly relevant dictionary that contains all passwords stored by the user in the Mac OS keychain.
Even if the dictionary attack doesn’t work right away, there are other helpful options available. By just looking at someone’s passwords you can get an idea on whether they reused a common password among multiple accounts, or had a specific pattern for memorizing their passwords. This information will help building a custom template or mask when performing a brute-force attack.
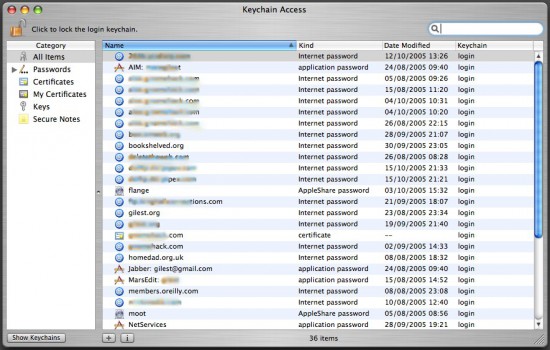
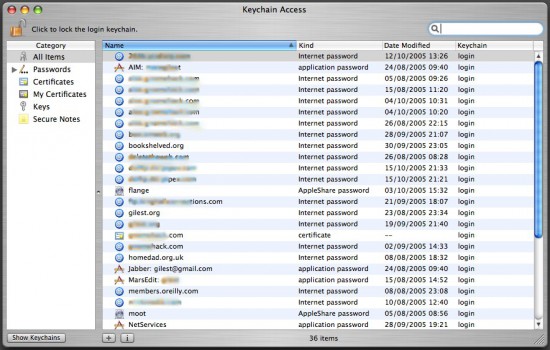
Using Apple Keychain Access
If you are using a Mac, you can get an idea of what sort of data is stored in the keychain. Just launch Keychain Access, a built-in tool available in every version of Mac OS, and you’ll see the list of passwords along with URLs (or application names), date and time, and other relevant information. When using Keychain Access, you’ll have to type your password every time when opening a new record, so using Keychain Access for an investigation is probably not the best idea.
Requirements to Extract Keychain Data
In order to use Elcomsoft Password Digger, you’ll need a Windows PC to run the tool, a set of keychain files extracted from the target Mac OS computer, and the user’s authentication information (Mac OS login and password or keychain password, if it’s different). For decrypting the system keychain, you’ll need a decryption key that must be extracted from the Mac OS computer (administrative privileges required).
System Keychain
- Keychain file extracted from the user’s Mac OS system
- Decryption key from the same system *
* The decryption key for system keychain must be extracted; administrative privileges are required if extracting from a live system
User Keychain
- Keychain file extracted from the user’s Mac OS system
- User’s local login password or keychain password (if different)
Obtaining Keychain Files
In order to decrypt the keychain with Elcomsoft Password Digger, the first thing you’ll need aside of the ElcomSoft tool is the keychain itself. In Mac OS, keychain is stored in several physical files. Yet another file holds the decryption key for the system keychain. You’ll need all of these in order to gain full access to encrypted information.
If you’re acquiring keychain files from a live Mac OS X system, do the following.
- Make a new folder on the desktop (e.g. “KEYCHAINS”).
- Open Terminal and issue the following command:cd Desktop/KEYCHAINS
- Copy the following files into the current folder ( “KEYCHAINS”):
cp /Users/<username>/Library/Keychains/login.keychain .
cp /Library/Keychains/System.keychain .
sudo cp /private/var/db/SystemKey .
Note that you need superuser access in order to extract SystemKey, a file that contains encryption metadata for decrypting system keychain. You’ll be prompted for apassword.Also note there is a final dot at the end of each “copy” command. This is not a formatting error; the dot means that the file is to be copied into the current folder (“KEYCHAINS” in our case).<user name> is the name of the user who’s keychain you are about to extract (currently logged in user is displayed before the “$” sign).
- Transfer the content of the “KEYCHAINS” folder to the Windows PC where you have Elcomsoft Password Digger installed. When Elcomsoft Password Digger prompts you for keychain location, point it to that folder.
If you have a disk image instead of the live system, extracting files is easier since you won’t need superuser access or admin password. Just mount the disk image and use your favorite file manager to copy the required files to your Windows computer.
Mounting the disk image is normally not a problem. If you’re dealing with a DMG image, Mac OS has built-in tools to mount it. If the disk image is in EnCase .E01 format, you’ll need to use third-party tools to mount the image.
Issues and Obstacles
The keychain is supposed to be secure, yet Elcomsoft Password Digger offers instant decryption. So is there something wrong with keychain security, or are we not telling something?
Well, in fact, there are certain obstacles that can make keychain acquisition and/or decryption difficult of impossible. If, for example, the disk is encrypted with FileVault2, we won’t be able to extract keychain files, so there will be nothing to decrypt.
Another potential issue is attempting to decrypt a user keychain with a missing password. Since Elcomsoft Password Digger requires a password to decrypt the keychain, there’s really nothing the tool can do if the password is not known. At this time, we are working to add the ability to break keychain passwords to Elcomsoft Distributed Password Recovery; we’ll post immediately when it’s ready.
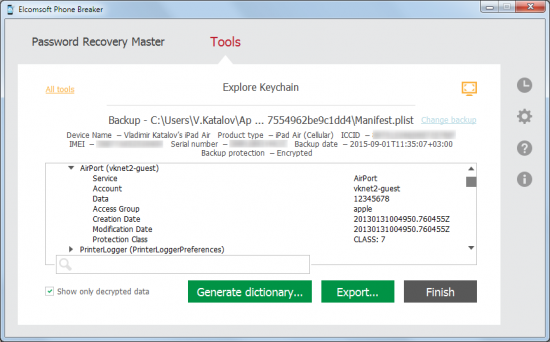
It’s Getting Better
Elcomsoft Password Digger is still new. Version 1.0 can only accept keychain files copied from a Mac OS X system. This very moment we’re working on building a native Mac OS version of the tool, and adding two alternative ways to acquire keychains:
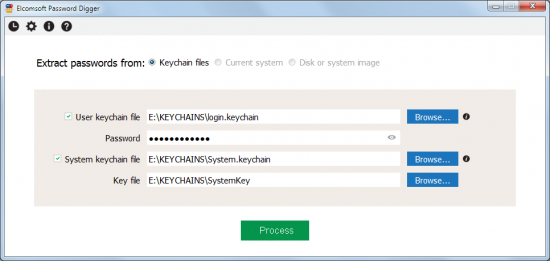
See the two greyed-out options? The native Mac OS tool will be able to extract keychain files automatically from the current system (if launched on the computer being investigated; administrative password required for extracting decryption key for the system keychain). Both Windows and Mac OS tools will be able to use an offline disk or mounted disk image to automatically locate and extract system and user keychains. The update will be free to those who purchase the initial edition.