As you may already know, we’ve added Android support to our WhatsApp acquisition tool, Elcomsoft Explorer for WhatsApp. While the updated tool can now extract WhatsApp communication histories directly from Android smartphones with or without root access, how do you actually use it, and how does it work? In this blog post we’ll be looking into the technical detail and learn how to use the tool.
WhatsApp on Android
WhatsApp claims over a billion users. The company has client apps for all major mobile platforms including Android, iOS and Windows 10 Mobile, yet 73% of its user base are Android users. Elcomsoft Explorer for WhatsApp was an iOS exclusive for way too long. Now it’s time to go Android!
Extracting WhatsApp Communication History from Android Devices
WhatsApp employs peer-to-peer exchange of encrypted messages, making the man-in-the-middle attack unfeasible. The company does not keep a copy of those messages anywhere on its servers, which rules out direct cloud acquisition. WhatsApp encrypts its cloud backups, which makes acquisition far from trivial.
If root access is available, we can use root privileges to access and extract the working database. If you have root access, Elcomsoft Explorer for WhatsApp can extract and decrypt the WhatsApp database from pretty much every Android smartphone running Android 4.0 through the latest 7.1.1 (up to 6.0.1 without root access).
If root access is not available, WhatsApp acquisition options become even more limited. You could use manufacturer’s backup tool to back up the content of the device; image the device or use a custom recovery (in a case of unlocked bootloader) to extract device content. However, Elcomsoft Explorer for WhatsApp offer a safer and easier alternative by forcing ADB backup of WhatsApp data and decrypting that backup. This only works for Android devices running Android 4.0 through 6.0.1.
If You Have a Rooted Device
If your Android device has root access, or if you can obtain root access, you’ll be able to access the data without much of an issue. If this is the case, Elcomsoft Explorer for WhatsApp will extract the WhatsApp database from its protected location and make a temporary copy in publicly accessible /sdcard. The next step is copying the data to a PC where Elcomsoft Explorer for WhatsApp is installed. After that, the temporary files are deleted.
For Non-Rooted Devices
With no root access, direct extraction of WhatsApp data is not possible. One must then use a local WhatsApp backup to extract data. However, recent versions of WhatsApp encrypt their backups (or disable them completely).
Elcomsoft Explorer for WhatsApp employs a smart workaround for processing WhatsApp extraction on non-rooted devices. This is how it works.
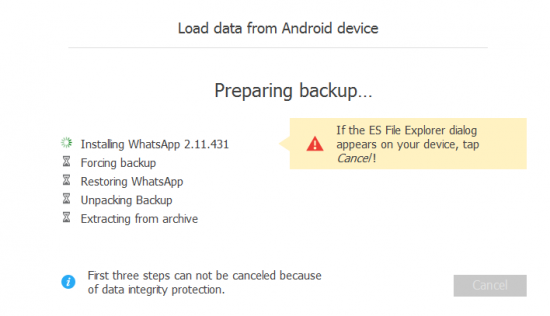
Elcomsoft Explorer for WhatsApp downloads WhatsApp v.2.11.431 from the official Web site. WhatsApp 2.11.431 was the last version of WhatsApp without forced backup encryption.
- The tool downgrades existing WhatsApp installation to v.2.11.431.
- Once WhatsApp 2.11.431, Elcomsoft Explorer for WhatsApp makes a WhatsApp backup via ADB. Note: if device storage is encrypted, the ADB backup will require a password. Use “pass123” as a password.
- Once the backup is created, Elcomsoft Explorer for WhatsApp pulls backup data from the device and restores the original version of WhatsApp.
Extracting WhatsApp from Android: The How-To Guide
That’s all great, but what do you actually do to extract a WhatsApp database from an Android smartphone? Since most Android devices don’t have root installed, we’ll put the most common scenario first.
Connect your Android smartphone to the PC. The smartphone can be isolated in a Faraday bag and/or put to Airplane mode.
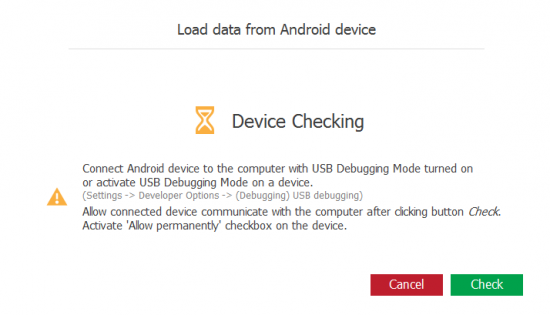
- In Elcomsoft Explorer for WhatsApp, use “Load from Device”. The tool will display step-by-step instructions you’ll have to follow on the phone. You’ll need to unlock the device, enable Developer Options and turn on ADB Debugging.
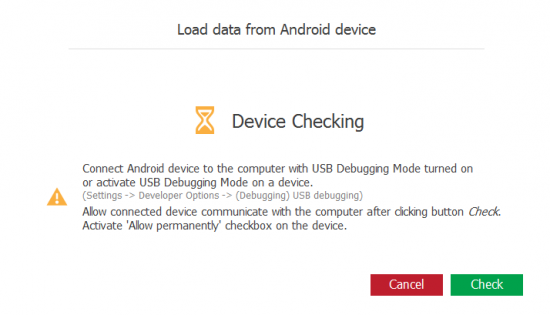
- Elcomsoft Explorer for WhatsApp will display the list of connected devices (considering that you have the correct drivers installed and ADB Debugging enabled).
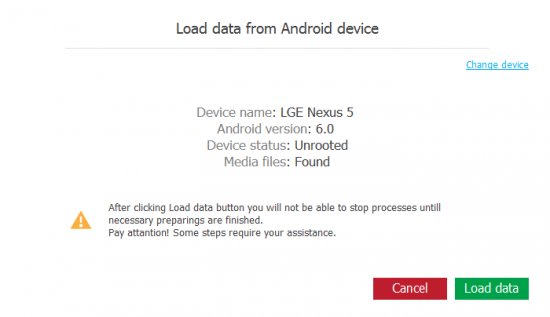
- Select the Android phone you are about to process. Elcomsoft Explorer for WhatsApp will display information about the device.
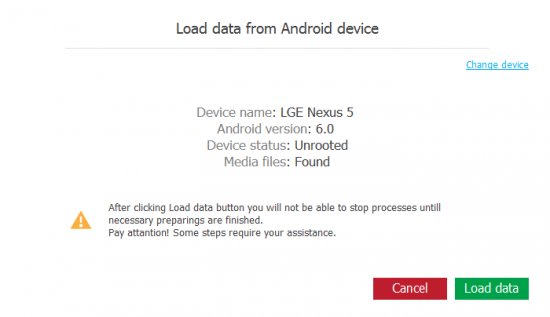
- Click “Load data” to begin the extraction.
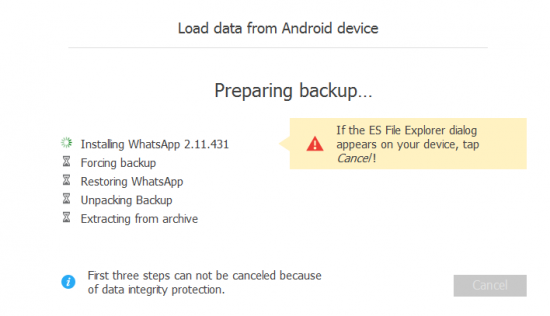 Note: once the “Forcing backup…” message appears you will need to confirm a backup prompt on the Android device.
Note: once the “Forcing backup…” message appears you will need to confirm a backup prompt on the Android device.
- Elcomsoft Explorer for WhatsApp will automatically import and display the data including Calls, Messages, Media and Contacts.
Load from Local Storage
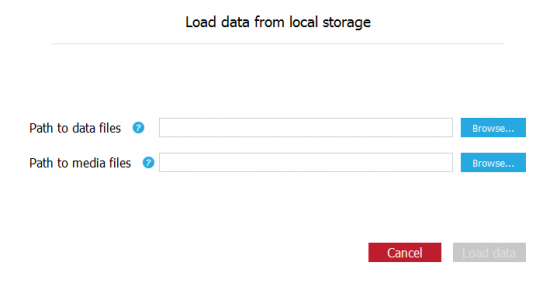
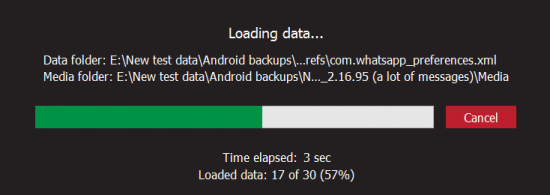
Elcomsoft Explorer for WhatsApp supports WhatsApp data extracted from Android devices in other ways (e.g. by booting into a custom recovery, imaging the device or performing chip-off acquisition). In this case, use the “Load from local storage command”.
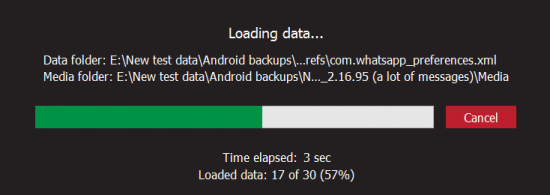
In order for Elcomsoft Explorer for WhatsApp to process external data, make sure to preserve the original data structure of WhatsApp backups. Broken or incomplete data sets may not be imported. You will need to specify path to com.whatsapp_preferences.xml extracted from WhatsApp sandboxed data as well as path to its “media” folder (extracted from the SD card).
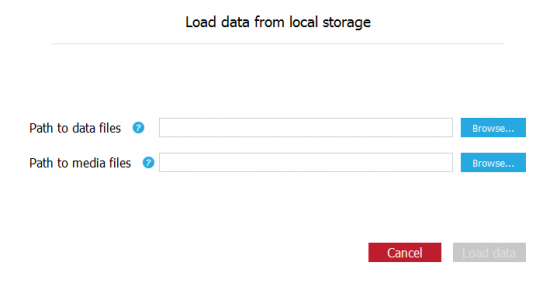
After that, you’ll be able to access the messages, contacts, call information and media files.