Obtaining information from a locked iPhone can be challenging, particularly when the device is passcode-protected. However, four critical pieces of information that can aid forensic analysis are the device’s International Mobile Equipment Identity (IMEI), Mobile Equipment IDentifier (MEID), MAC address of the device’s Wi-Fi adapter, and its serial number. These unique identifiers can provide valuable insights into a device’s history, including its manufacture date, hardware specifications, and carrier information.
Elcomsoft iOS Forensic Toolkit 8.20 for Mac and 7.80 for Windows now includes a new mechanism for low-level access, which enables the extraction of certain parts of the file system from the latest Apple devices. This partial extraction raises questions regarding what data can and cannot be extracted and how missing information can be accessed. Learn about the partial file system extraction, its benefits and limitations.
Welcome to part 2 of the Perfect Acquisition series! In case you missed part 1, make sure to check it out before continuing with this article. In this section, we will dive deeper into iOS data protection and understand the obstacles we need to overcome in order to access the data, which in turn will help us accomplish a Perfect Acquisition when certain conditions are met.
Forensic acquisition has undergone significant changes in recent years. In the past, acquisition was relatively easy, with storage media easily separable and disk encryption not yet widespread. However, with the rise of mobile devices and their built-in encryption capabilities, acquiring data has become increasingly challenging. Traditional approaches like disk dumps are no longer feasible, and software exploitation has become the industry standard. Despite these methods, there are limitations to mobile acquisition, including the need to collaborate with the device, the possibility of hardware defects or deliberate data tampering. As a result, there is a need for continuous innovation in forensic acquisition to address these challenges and ensure accurate and reliable data collection.
The first-generation HomePod is a smart speaker developed by Apple that offers high-quality audio and a range of features, including Siri integration and smart home controls. However, as with any electronic device, it can store valuable information that may be of interest in forensic investigations. In this article, we will explore how to use the forensically sound checkm8 extraction to access data stored in the HomePod, including the keychain and file system image. We will also outline the specific tools and steps required to extract this information and provide a cheat sheet for those looking to extract data from a HomePod. By the end of this article, you’ll have have a better understanding of how to extract data from the first-generation HomePod and the potential limitations of this extraction method.
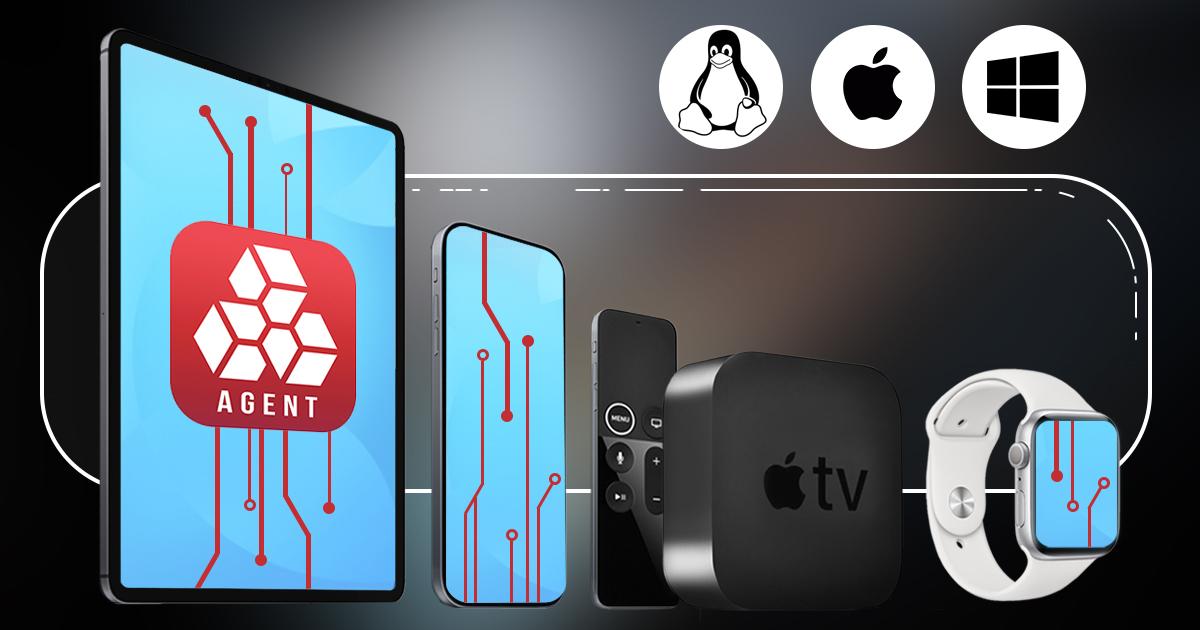
Agent-based low-level extraction of Apple mobile devices requires sideloading an app onto the device, which is currently far from seamless. One can only run sideloaded apps if they are signed with a device-specific digital signature, which must be validated by an Apple server. Establishing a connection to the server carries a number of potential risks. In this article, we are proposing a solution that reduces the risks by using a firewall script.
In this article, we will discuss how to access the hidden port of the first-generation HomePod and extract its file system image. Note that this process requires disassembly, voids the HomePod warranty, and requires specific tools, including a custom 3D-printable USB adapter, a set of screws, and a breakout cable. Therefore, this method is not recommended for casual users and should only be used by professionals who have a thorough understanding of the process.
Dictionary attacks are among the most effective ones because they rely on the human nature. It is human nature to select passwords that are easily memoizable, like their pet names, dates of birth, football teams or whatever. BBC counted 171,146 words in the English dictionary, while a typical native speaker (of any language) knows 15,000 to 20,000 word families (lemmas, or root words and inflections). Whatever the attack speed is, it will not take too much time to check all the English words.
In the previous article we discussed the different methods available for gaining access to encrypted information, placing password recovery attacks at the bottom of the list. Password recovery attacks are one of the methods used to gain access to encrypted information. In this article we’ll discuss the process of building a password recovery queue. Learn how to choose the appropriate workflow for the attack, the first prioritizing files with weaker protection, the second prioritizing faster and shorter attacks, and the third being a combination of the two. For your reference, we built a table to compare the relative strength of different file formats and encryption methods, helping users prioritize their attack queues.