iOS backup passwords are a frequent topic in our blog. We published numerous articles about these passwords, and we do realize it might be hard for a reader to get a clear picture from these scattered articles. This one publication is to rule them all. We’ll talk about what these passwords are, how they affect things, how to recover them, whether they can be reset, and whether you should bother. We’ll summarize years of research and provide specific recommendations for dealing with passwords.
iOS Backups: What Are They?
Within the Apple ecosystem, user data can be backed up in several different ways, with some redundancy. Here’s what is available:
- iCloud backups: these can be either plain or encrypted if Advanced Data Protection for iCloud is enabled.
- iCloud synchronized data: partially redundant, partially complementary to iCloud backups. E.g., the camera roll may be synchronized with iCloud via iCloud Photos, and may not be included in iCloud backups.
- Local backups: created on the user’s computer with iTunes or Finder. These can be plain or encrypted (password-protected).
Note: The only iOS-based devices that have the backup service are the iPhone, iPad, and iPod Touch. All other iOS-based devices such as the Apple TV, Apple Watch, and HomePod, do not have a backup service. For those devices, advanced logical extraction is limited to extended device information, crash logs, and media files.
In addition to backups, which are extracted in the course of logical analysis, significantly more data may be available if a low-level extraction method is available for a given device. For older devices, checkm8-based extraction is available, while many iOS versions are supported by a different low-level method utilizing the extraction agent. Despite being able to extract much more information than is available in backups, these methods are limited in their scope due to either supporting outdated devices or older versions of iOS. Meanwhile, logical analysis (and thus backups) is available for all iPhone and iPad devices regardless of the OS version.
Device backups may contain valuable evidence; they are your best bet when performing logical acquisition. Apple’s documentation lists the data that is not included in local backups:
A computer backup of your device, which is not the same as a sync, includes almost all of your device’s data and settings. A backup from a computer doesn’t include:
- Content from the iTunes and App Stores, or PDFs downloaded directly to Apple Books
- Content synced from your Mac or PC, like imported MP3s or CDs, videos, books, and photos
- Data already synced and stored in iCloud, like iCloud Photos, iMessages, and text (SMS) and multimedia (MMS) messages
- Face ID or Touch ID settings
- Apple Pay information and settings
- Apple Mail data
- Activity, Health, and Keychain data (to back up this content, you’ll need to use Encrypted Backup.)
We have a note on the Camera Roll though.
Local Backups, iCloud Photos and Camera Roll
While Apple states that data already stored in iCloud (e.g., iCloud Photos) will not be included in local backups, our own tests do not confirm it. Based on our research, the Camera Roll is always included in local backups regardless of whether or not iCloud Photos are used. However, some pictures may be physically removed from the device if “Optimize iPhone Storage” is enabled. According to the documentation, “when Optimize Storage is turned on, full-resolution photos and videos are stored in iCloud, and, when needed, space-saving copies are stored on your device.” If this occurs, full versions of photos can be extracted from iCloud through cloud extraction using Elcomsoft Phone Breaker.
Photos along with metadata can be extracted from the device via the AFC protocol with Elcomsoft iOS Forensic Toolkit during of advanced logical acquisition. This method has an additional advantage: the AFC protocol cannot be password-protected. Using AFC extractions makes sense in the following situations:
- The backup is password-protected; cannot reset or recover the password.
- The backup creation fails.
- You only need photos and nothing else.
What is a Backup Password?
Producing Backups
The Password is Empty
As we figured, one can extract more information from a password-protected backup. If the password is empty and you use iOS Forensic Toolkit for extraction, the tool will automatically attempt to set the password to “123”. Watch the phone screen; you’ll need to key in its screen lock passcode to confirm password change. Note: the passcode request is displayed for a limited time (about 30 seconds); pay close attention to the device screen! If you miss this request, the backup will continue to be created without a password. In this case, you will need to repeat the extraction, setting the password manually with a special command (see the “cheat sheet” above, step 7).
Removing the temporary password after the extraction also requires entering the screen lock code on the device screen. The prompt will appear for a short time at the end of the process, so it’s quite easy to miss it. If you miss the prompt, the backup still be created, but the phone will be configured with a backup password. When you try making a backup another time, you’ll encounter an “unknown password”. Moreover, third-party tools are doing the same, and each tool sets has its own password. Therefore, if you have a device with a backup password set, start by trying the passwords commonly used in forensic software packages.
Temporary Passwords Set by Forensic Tools
We are listing all known temporary passwords below:
- Elcomsoft iOS Forensic Toolkit: 123
- Cellebrite UFED: 1234
- MSAB XRY: 1234
- Belkasoft Evidence Center: 12345
- Oxygen Forensic: 123456 (or oxygen for legacy versions)
- Magnet AXIOM: mag123
- MOBILedit Forensic: 123
So there are six commonly used passwords: 123, 1234, 12345, 123456, mag123, oxygen. You can try them on new and existing backups, or even add them to the beginning of your custom dictionary.
Handling Unknown Passwords
The primary ways to handle backup passwords are: discovery, recovery, reset, bypass, and ignore.
Discovery
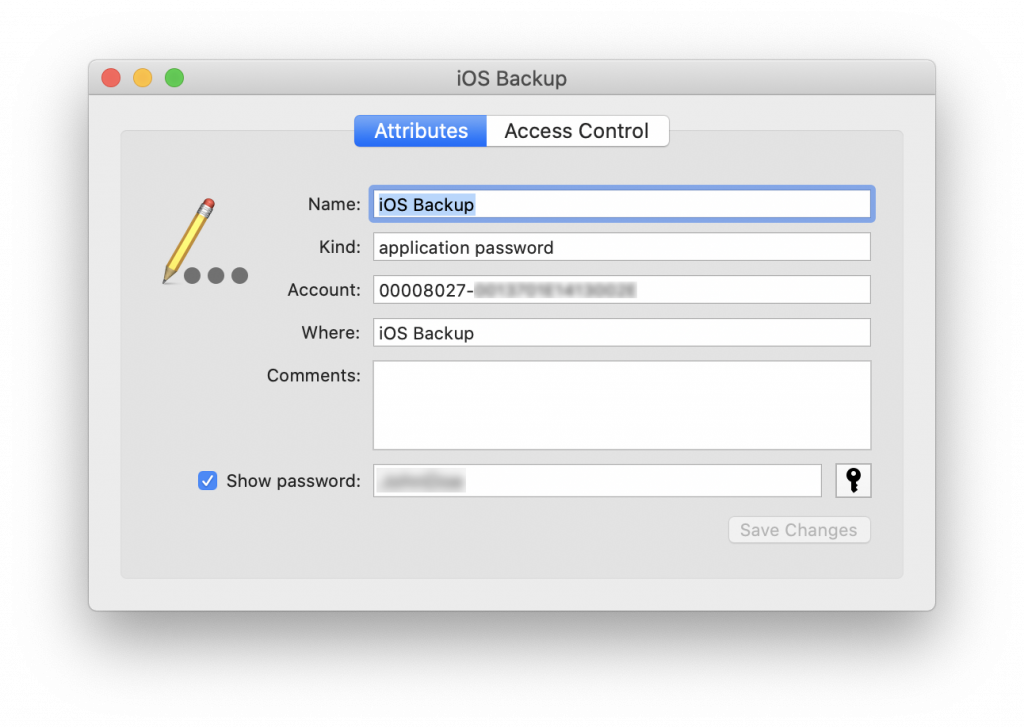
If you have access to a macOS computer paired to the subject iPhone, you may check the macOS Keychain for the backup password. Accessing the keychain requires the user’s Mac account password.
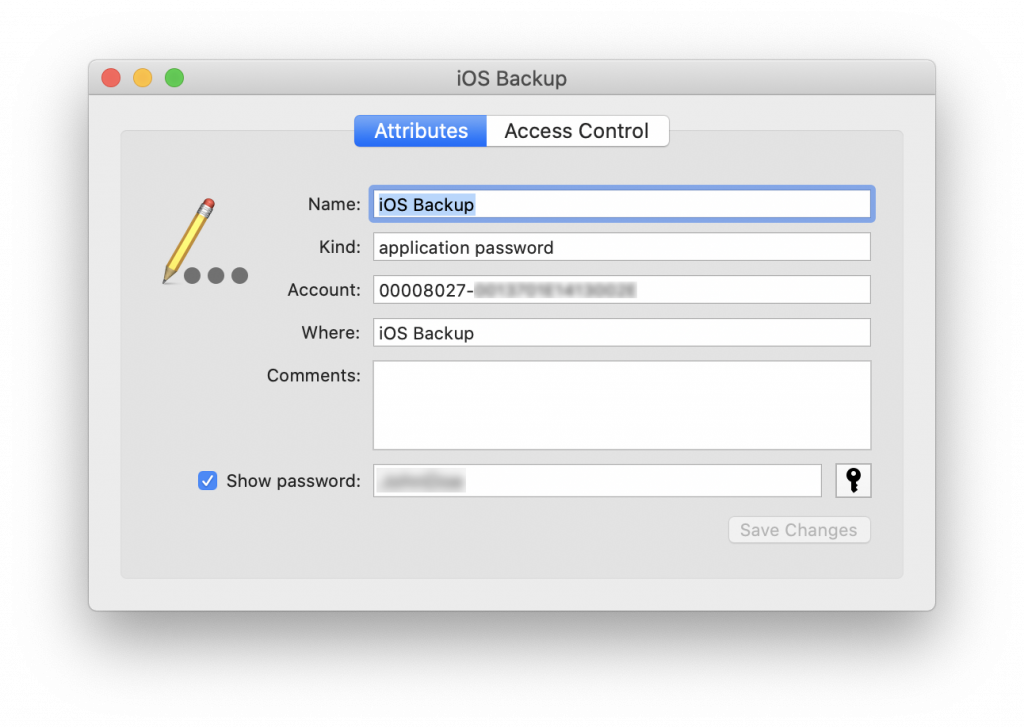
Software: Keychain Acccess (free; built-in to macOS)
For users of other operating systems, the iOS backup password may coincide with one of the user’s other passwords, which, in turn, can be extracted from sources such as the user’s Web browser or password manager. Passwords from the user’s browser can be extracted using Elcomsoft Internet Password Breaker, which supports all popular versions of Chrome, Edge, Firefox, Opera, and many others.
Recovery
The only way to break an iOS backup password is through a password recovery job utilizing brute-force or dictionary attack. However, even with powerful GPU accelerators, processors, a full-scale brute force attack would be extremely slow and generally unfeasible. Even with a fast GPU, you can only expect the speed of a few dozen passwords per second. Clearly, this method can only find the shortest passwords. We recommend using a short, custom dictionary targeting the human factor. Known user passwords, password leaks and smart attacks are all available in Elcomsoft Distributed Password Recovery. Passwords extracted from the user’s Web browser would make a good starting point for such attacks.
If you would rather use Elcomsoft Phone Breaker for attacking the backup password, note that password recovery is only supported in the Windows edition.
Reset
Начиная с iOS 11, пароль к резервной копии можно сбросить; подробные инструкции – в статье Логический анализ iPhone: резервные копии iTunes. Сброс пароля к резервной копии осуществляется через настройки, пункт Reset All Settings (потребуется ввести код блокировки экрана). Помимо пароля к резервной копии эта команда сбросит и код блокировки экрана устройства, а вместе с ним – удалит те данные, которые зависят от наличия на устройстве кода блокировки. Пропадёт список транзакций Apple Pay, учётные записи Exchange и вся переписка в них, а также многие другие данные. По этой причине сброс пароля – крайняя мера, идти на которую стоит лишь после тщательной оценки всех “за” и “против”.
Кроме того, сброс настроек, помимо перечисленных выше неприятных последствий, отключает “полётный” режим, что может вывести устройство в онлайн со всеми сопутствующими рисками. По этой причине сброс настроек рекомендуется проводить в изолированном от радиочастот помещении или внутри клетки Фарадея.
Кстати, далеко не факт, что пароль удастся сбросить, даже если вы знаете код блокировки экрана. Политики безопасности и политики MDM, ограничения “Экранного времени” и некоторые другие настройки могут запрещать (внимание!) удаление кода блокировки экрана. Но сброс настроек через пункт Reset All Settings всегда сбрасывает и код блокировки; следовательно, внешние настройки безопасности запрещают использование этой команды. И если с паролем “Экранного времени” можно попробовать что-то сделать, то внешние политики безопасности могут быть вне вашего контроля.
В то же время пароль вовсе не обязательно нужно сбрасывать: его можно попробовать… обойти.
Bypass
More capable low-level extraction methods are available for older devices up to iPhone 8/8 Plus/iPhone X running iOS up to version 15 inclusive, as well as for all devices (including iPhone 8/8 Plus/iPhone X) running iOS versions up to 16.6.1 inclusive (at the time of this writing). For legacy iPhone models, unconditional physical extraction is available regardless of the screen lock. Any of these low-level methods, among other things, will also extract the backup password (from the device’s keychain). While there is no sense in making a new backup after you pull low-level extraction, such passwords may grant access to older backups created.
checkm8 extractions
For iPhone 5s to iPhone 8/8 Plus/iPhone X, you can use forensically sound checkm8 extraction (cheat sheet). Note: if the iPhone 8/8 Plus/iPhone X is running iOS 14 or 15, you’ll also need to remove the screen lock passcode for checkm8 to work. checkm8 extractions are unavailable for iPhone 8/8 Plus/iPhone X devices running iOS 16. In these cases, use the extraction agent instead.
Agent-based extractions
The extraction agent (cheat sheet, installation instructions) works on any iPhone or iPad if the device is running one of the supported iOS versions (currently, all versions from 12 to 16.6.1 inclusive are supported; older versions are supported with checkm8). This is a powerful low-level extraction methods that does not require removing the screen lock passcode.
Ignore
If none of the above worked, there’s only one option left: ignore the password and move on. You can still extract the entire Camera Roll, and you won’t need a password for that. You can also extract system logs, application data, and extended device information without needing the password.
One More Thing
Any low-level extraction method will, among other things, unveil the backup password. Creating a new backup after employing a low-level method is pointless; the backup won’t contain any new data. However, the password can be useful for decrypting existing, older backups found on the user’s computer.