We also trust these companies in ways that we do not understand yet. How many of you trust Apple? No voting… Just me 🙂 Damn! OK. May I ask you a very good question. Trusting to do what? Trusting when they say: “iMessages are end-to-end encrypted”? I mean, with all of that massive security engineering, to make sure it’s as good as it can be, so they genuinely believe they’ve done that. I do, generally, they’re great people. But… people believe themselves they can defend themselves against the Russians. If the Russians specifically targeted Apple, it’s only they can defend themselves. – Ian Levy, director at the GCHQ on anniversary of the foundation of the FIPR event that was held on 29/04/2018).
This is probably just a co-incident, but “the Russians” are concerned about iCloud security, too.
iCloud is one of the best components of Apple ecosystem. It takes zero effort to set up, and it’s extremely convenient, lightning fast, and works transparently to the user. However, it has multiple security and privacy concerns, and we feel the situation is getting out of hands.
iCloud Backups, Syncing and Data Storage
Apple iCloud was introduced back in 2011, along with iOS 5, and gave iPhone users a great feature Android fans could only dream about at the time: iCloud backups. Even today, almost 7 years later, Android backups still pale in comparison.
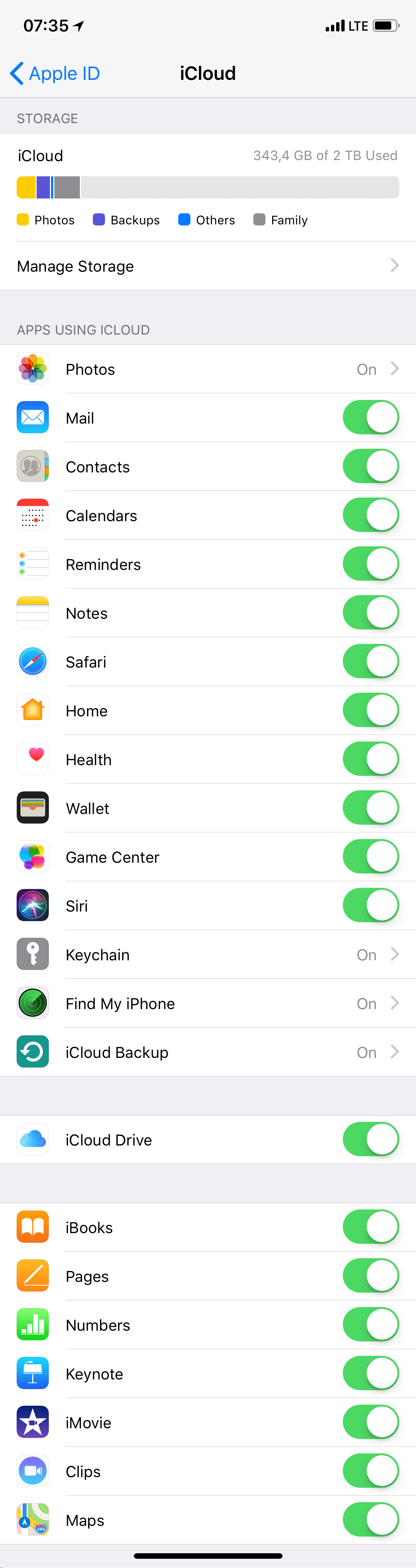
iCloud delivers many different services; the backups are just one of the features. Yes, we are speaking of data syncing. You can simply open Settings | {Apple ID} on your iOS device to see the list of of system services and built-in apps that are using iCloud.
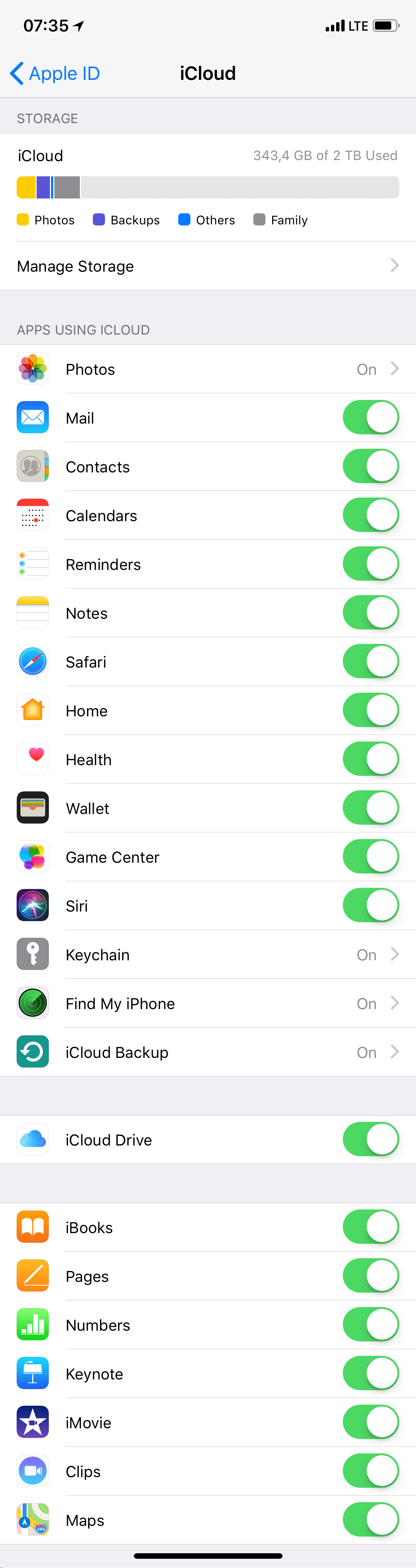
We will get back to this list later, as it needs some explanations. There is still more; for example, with Apple CloudKit, any third-party app can use iCloud to make its own backups (for example, apps such as 1Password, WhatsApp, Viber and many others).
Do we need to worry? In fact, yes we do.
The Types of Synced Data
Despite the name (“Apps using iCloud”), these settings have a slightly different meaning. The “On” switch means that almost all data from a given app or service is being synced across all your devices registered on the same account. And of course, the data is actually stored in iCloud, so the “using iCloud” moniker is somewhat misleading.
This list is not complete. During its WWDC keynote speech, Apple announced that in macOS Mojave, we are are going to have News, Stocks, Voice Memos and Home available on the Mac. This means that these apps will sync their data through iCloud.
To tell you the truth, the Stocks category has been synced even in iOS 11 – there was just no user-selectable option for that. Thanks God, now you have a bit more control.
There is something else that is being synced since at least iOS 10: call history (including FaceTime) and Weather. I don’t care about Apple knowing how I use the Weather app, but I never asked to upload information about my phone calls to the cloud, making them accessible to TLA.
GDPR
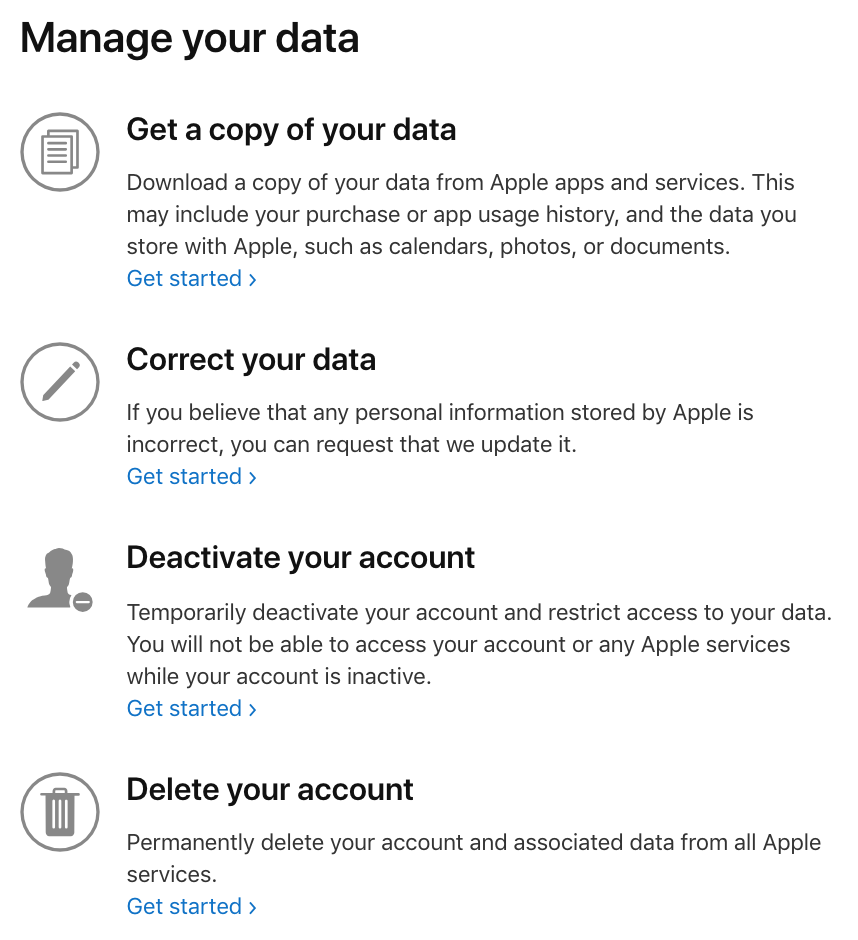
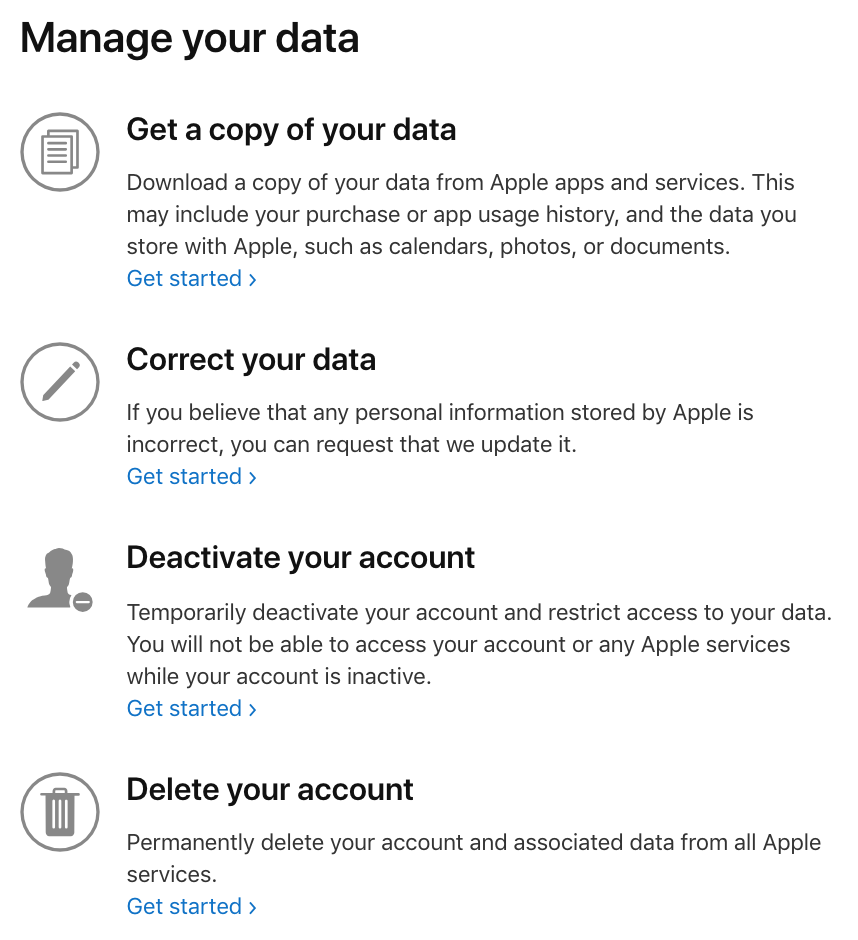
Under the new EU legislation, users now have the right to review what companies know about them, access that data or request to delete some of all of it. Apple now offers that, too via their Data and Pricacy page:
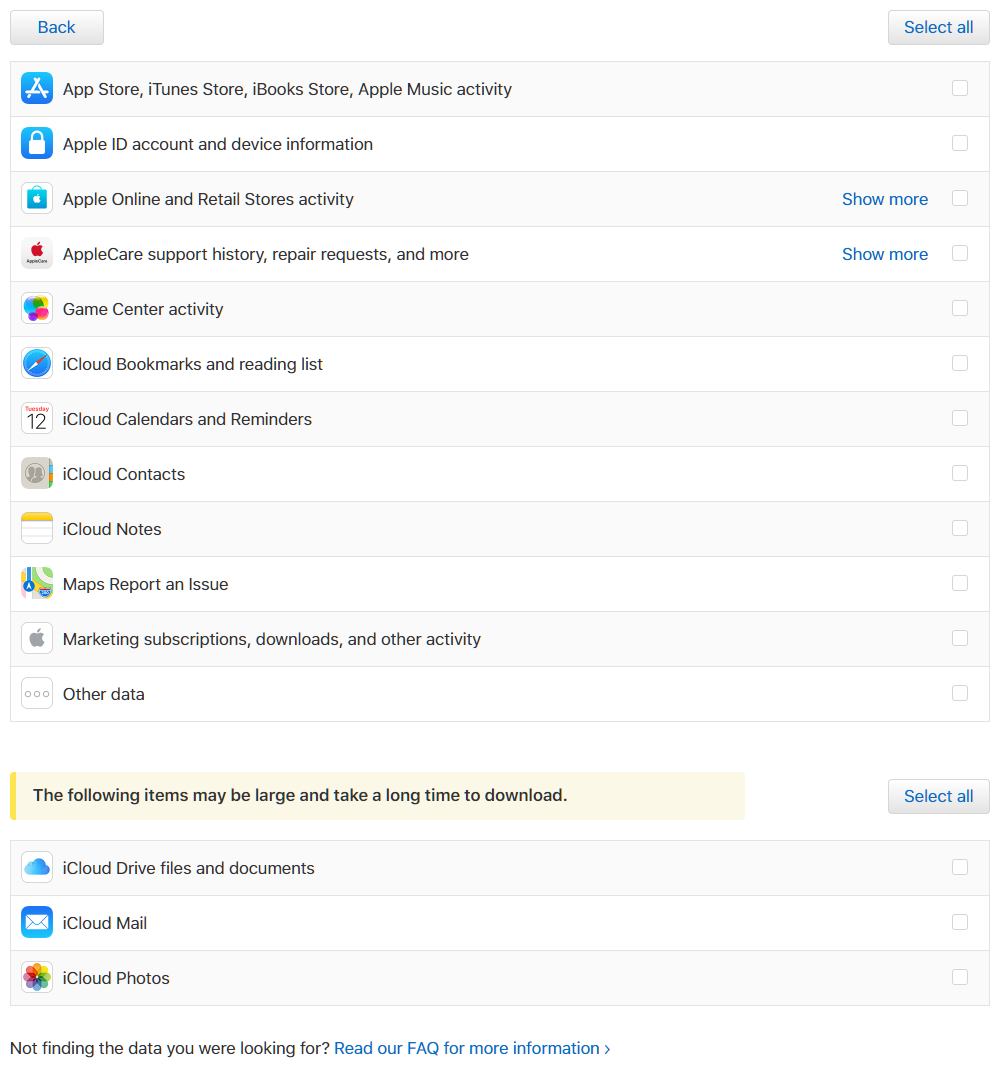
Here is what you can select to download (there is also iCloud Drive files and documents, iCloud Mail and iCloud Photos).
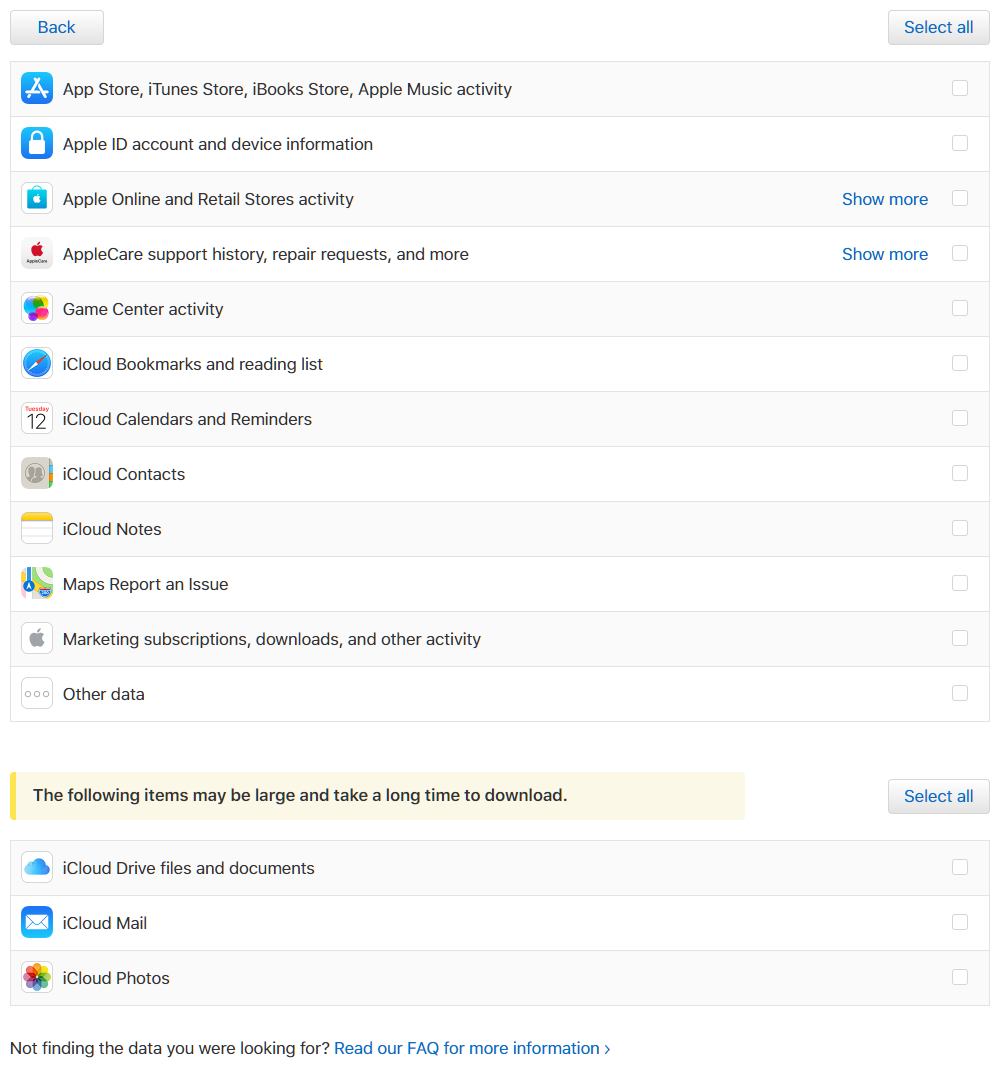
Don’t you think that the number of data categories is a bit… limited? We know for sure that Apple collects far more categories than those listed here. Well, the most interesting data is hidden under Other data. In particular, the call history will be stored there. As we already mentioned, there is no option to disable call history syncing. To address the potential privacy issue, Apple added an explanation at Get a copy of the data associated with your Apple ID account:
Q: Why does Apple store my call history?
A: When you’re signed in to iCloud with your Apple ID on multiple devices, your call history is stored and synced to allow you to return calls from any of your devices. Apple doesn’t access or use this information for any other purpose. You can turn off this feature by turning off iCloud Drive in iCloud settings.
Really? In fact, the calls are synced even if the Allow Calls on Other Devices option is disabled. I do not care about the actual purpose, but I really need to have control over this whole synchronization thing without disabling Apple Drive completely (which is not a proper solution as it just creates more problems to system functionality and troubles thousands third-party apps).
The same documents explains why some specific data is not available:
Any data that isn’t provided is either in a form that is not personally identifiable or linked to your Apple ID, is stored in an end-to-end encrypted format that Apple cannot decrypt, or is not stored by Apple at all. Additionally, some data may have been held only for a very short time and is no longer on our servers.
Particularly iMessages:
Q: Why don’t I see my Messages content as part of my data request?
A: Your messages are encrypted on your device and can’t be accessed by anyone without your device passcode.
Is it really so? Also, does that really matter in GDPR context that the data is encrypted and only its owner has the password (or whatever) to decrypt it?
iCloud Data Encryption
iCloud security overview (https://support.apple.com/en-us/HT202303) is a good point to start:
End-to-end encryption provides the highest level of data security. Your data is protected with a key derived from information unique to your device, combined with your device passcode, which only you know. No one else can access or read this data.
These features and their data are transmitted and stored in iCloud using end-to-end encryption:
- Home data
- iCloud Keychain (Includes all of your saved accounts and passwords)
- Payment information
- Siri information
- Wi-Fi network information
To use end-to-end encryption, you must have two-factor authentication turned on for your Apple ID. To access your data on a new device, you might be required to enter the passcode for an existing or former device.
Sounds good. I have no idea why Health data is not on the list (I believe it should be protected stronger than the Home data). Also, making end-to-end encryption only available with Two-Factor Authentication is a bit of a strange decision. In fact, you can set up and use the iCloud Keychain without 2FA.
Anyway, what about the messages? There is a special note in the same document:
Messages in iCloud also uses end-to-end encryption. If you have iCloud Backup turned on, a copy of the key protecting your Messages is included in your backup. This ensures you can recover your Messages if you’ve lost access to iCloud Keychain and your trusted devices. When you turn off iCloud Backup, a new key is generated on your device to protect future messages and it is not stored by Apple.
The point is: even if Apple does not mention it, the encryption key for iMessages is stored in iCloud Keychain. In order to get access to the keychain, one has to know the passcode to one of the devices in the “trusted circle”. But what if you (the legitimate user of your own iCloud account) lose access to your trusted device(s) and so lose access the keychain? If that happens, how can you get your messages back on your new device?
Apple seems to have thought about it. If you have iCloud backups enabled, the encryption key for iMessages will be stored in the backup. Now, let’s look more closely at this one.
If the “Messages in iCloud” option is enabled, the messages themselves are NOT included in iCloud backups. The encryption key, however, will be included and accessible by Apple (like the rest of the iCloud backup) and so available to the law enforcement.
Once again: the encryption key allowing to decrypt iMessages is stored both in iCloud Keychain *and* in iCloud backups (which are inherently much less secure).
May be the encryption key in iCloud backups is end-to-end encrypted? Seems not; otherwise it would have the same protection level as the keychain, while we know that it cannot be recovered in this specific situation. So, once again: the iMessage encryption key is saved in iCloud backups, and can be restored without any trusted devices for your convenience – even if you explicitly disabled “Messages in iCloud”. Maybe you should know the passcode to get the key, too? Or you can restore messages only to the same device (you created iCloud backup from)? Well, we will definitely make some research on that and share the result with you. There are two possibilities: either the implementation is not really secure (and you messages can be ready by 3rd party, whoever it is); or it is not convenient to you as a user, and in some cases you will not be able to restore your messages from backup.
In the meantime, the new version of our Elcomsoft Phone Breaker is able to download and decrypt messages from iCloud. You will need the Apple ID, the password, the second factor (the code from SMS or push notification) and the passcode of one of the trusted devices; see our other blog posts with details.
Again, “How many of you trust Apple?”
Security, privacy and convenience. As usual, you never get all three.