In early July, 2017, Apple has once again revised security measures safeguarding iCloud backups. This time around, the company has altered the lifespan of iCloud authentication tokens, making them just as short-lived as they used to be immediately after celebgate attacks. How this affects your ability to access iCloud data, which rules apply to iCloud tokens, for how long you can still use the tokens and how this affected regular users will be the topic of this article.
The History of iCloud Authentication Tokens
iCloud authentication tokens are used to spare the user from re-entering their Apple ID credentials every time they want to access iCloud services. For many years, we’ve been able to use authentication tokens in Elcomsoft Phone Breaker to bypass standard authentication procedures, including two-factor authentication. We could use tokens to download backups, access synchronized data and pull files from iCloud Drive.
- Initially (a long time ago), iCloud authentication tokens did not carry an expiration date. You could use an authentication token for ages or until the user changed their iCloud passwords.
- Soon after celebgate scandal, Apple dramatically limited tokens’ lifespan. For the first time ever, the company implemented a two-sided approach. The same authentication token could be valid and expired at the same time. While you could still use the token for accessing some types of data (including synchronized information), the same token could only be used to access iOS system backups within just one hour after authenticating with Apple ID login and password.
- In iOS 9 and newer, Apple moved system backups from ‘classic’ iCloud to iCloud Drive. All lifespan restrictions were removed; you could now continuously re-use authentication tokens to access everything in iCloud (including backups, synced data, iCloud Photo Library etc.)
- Finally, in July 2017, Apple once again decided to restrict the lifespan of authentication tokens. We are now back to step 2, with authentication tokens at the same time being ‘valid’ for some times of data and ‘expired’ for the purpose of obtaining system backups. The exact lifespan is believed to be in the range of 12 hours.
The Problem
This new stance caused a problem in Elcomsoft Phone Breaker. If an expired token was used, or if you simply pulled previously saved authentication credentials from EPB cache, you would be able to access everything but backups; all this without a proper error message or the way out.
The New Order
We now once again live in the age of expiring iCloud tokens, so we updated Elcomsoft Phone Breaker accordingly. Version 6.61 can now correctly identify and process tokens with lifespan restrictions. You will now be prompted to either re-authenticate with Apple ID login and password or continue using existing authentication token for the purpose of accessing synchronized data and files in iCloud Drive.
From now on, the following expiration time applies to iCloud tokens:
- System backups (all versions of iOS): 12 hours
- iCloud Drive data: unlimited, tokens unaffected
- Synchronized data: unlimited, tokens unaffected
- iCloud Photo Library (all versions): unlimited, tokens unaffected
In practical terms, this means that the same authentication token extracted from the suspect’s computer or pulled from Elcomsoft Phone Breaker’s cached credentials storage could have already ‘expired’ for the purpose of accessing iOS system backups while still ‘valid’ for the purpose of downloading synchronized data (such as call logs, calendars, notes etc.) and obtaining data from iCloud Drive.
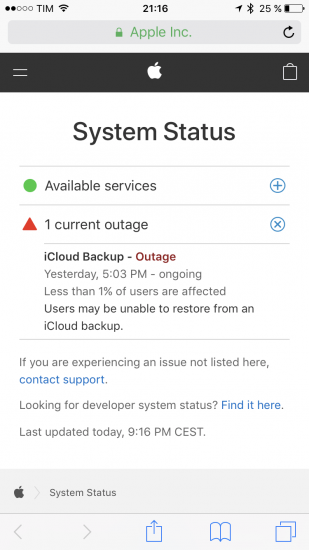
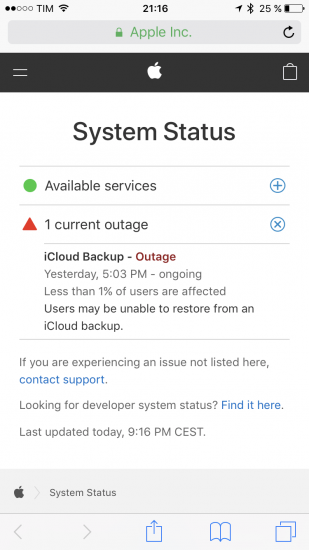
Effects on End Users: iCloud Outage
Since the end of June, iCloud had a series of outages affecting a large number of users. While official sources mentioned problems affecting only 0.1% of all users, independent reports suggested otherwise. While we don’t know if this outage is connected with new security measures, we find it very likely as continuous re-authentication attempts could have put enough stress on Apple’s authentication servers to cause denial of service errors.
Conclusion
Apple has once again altered the rules. While this change broke old versions of Elcomsoft Phone Breaker, we released a fix quickly, making it available free of charge to everyone with an active service contract (this also includes everyone who bought an Elcomsoft Phone Breaker license less than a year ago).