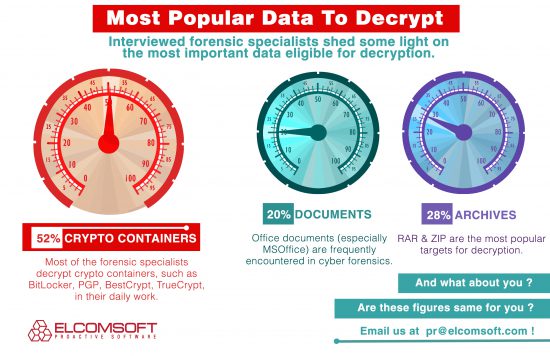
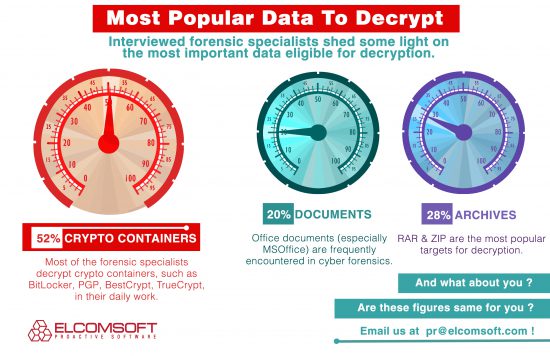
How often do you think forensic specialists have to deal with encrypted containers? Compared with office documents and archives that are relatively infrequent, every second case involves an encrypted container. It may vary, but these evaluations are based on a real survey conducted by our company.
It is hard to overestimate the importance of the topic. In the first part of our story we discussed the way of getting access to encrypted volumes using an encryption key. Now, let’s see which other ways can be used.
Unlike Elcomsoft Forensic Disk Decryptor, Elcomsoft Distributed Password Recovery does not search for existing decryption keys. Instead, it tries to unlock password-protected disks by attacking the password. The tool applies an impressive variety of techniques for attacking the password. In this case, the whole disk encryption scheme is only as strong as its password. Fortunately, the tool can execute a wide range of attacks including wordlist attack, combination attacks, mask attacks, smart attacks and so on and so forth, with advanced GPU acceleration and distributed processing on top of that. The whole sophisticated arsenal comes in particularly handy if we speak about more or less secure passwords.
Check this video guide to learn more about setting and distributing attacks within network https://www.youtube.com/watch?v=9nEqTAviAVI
You may have another fair question: how do we actually attack the encrypted disk or volume? Do we need to manipulate with the whole encrypted disk that may contain terabytes of information? Well, partly. We only need certain bits of data involved in the password encryption procedure. And in this very situation we can use a companion tool called Elcomsoft Disk Encryption Info (EDEI for short) that comes together with Elcomsoft Distributed Password Recovery. The little tool easily gets the necessary data from crypto containers in order to later feed it to EDPR installed on a computer, suitable for password recovery (I’ll tell you later what I mean).
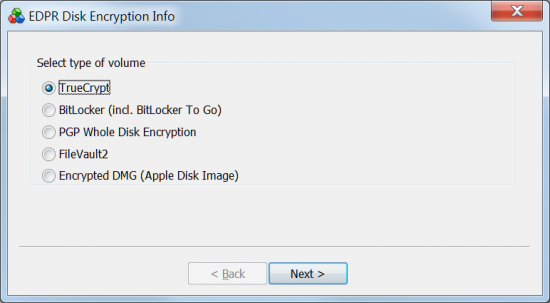
So, our little helper called EDEI can detect encrypted disks and volumes that you want to decrypt. You can just choose the necessary type of crypto container. The program shows you a range of all supported crypto-containers. Recently, we added support for FileVault 2 and DMG containers.
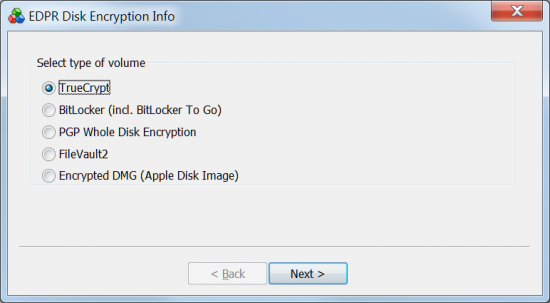
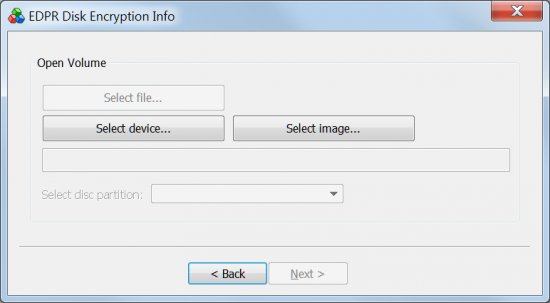
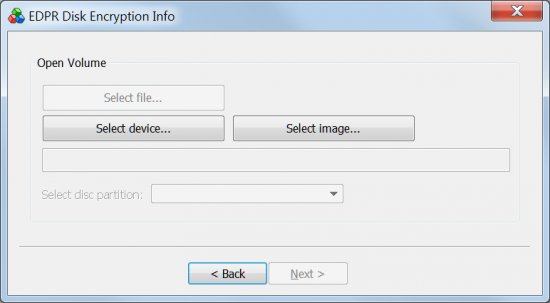
After selecting the type of the crypto container, select between File, Device or Image as source of encrypted data. These may be different for the different types of crypto containers. In case of an encrypted device you can also specify its partition, if the only partition has been encrypted.
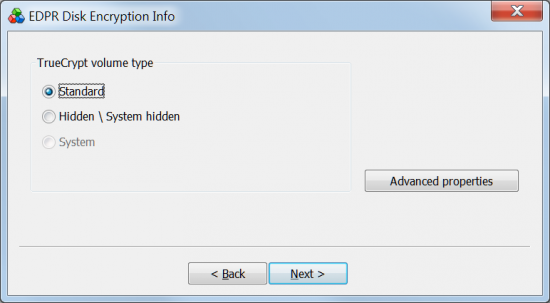
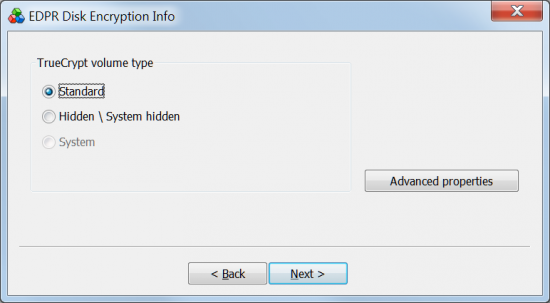
In case of TrueCrypt you can also choose whether a container is hidden or not.
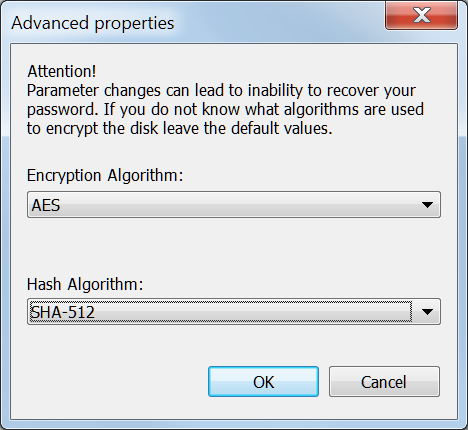
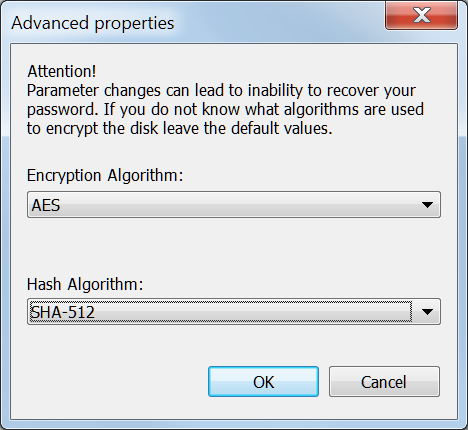
Now, if you go to Advanced properties, you can help by specifying the encryption algorithm and hash algorithm that were used in the encrypted volume, but only if you know them. Otherwise leave the settings as default to let the program define it for you.
Once the required data is taken from the crypto container, you can switch to Elcomsoft Distributed Password Recovery and chase the game there.
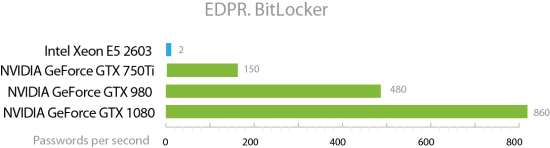
What would be the fastest PC to break passwords? You’ll want one or several video cards. A single high-end video card such as an NVIDIA GTX 1080 can speed up the attack at least by a factor of 100 (without overclocking). Yes, a single GTX 1080 board will break passwords one hundred times faster than even the fastest Intel CPU you can get your hands on.
Prejudiced against video cards? You can easily build a network of 100 computers to match it! Granted, this will cost you 100 times more than said video card, and you’ll need a big room, and you’ll pay for electricity and air conditioning, but hey – the 100 computers each equipped with a bunch of GTX 1080 boards will be faster than supercomputers used by NASA (and we’re not exaggerating).
These acceleration tricks can contribute to retrieving passwords for crypto containers where an extremely strong encryption is involved.
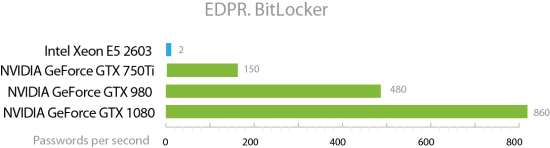
In case of BitLocker encryption you will really need to build a good wordlist and squeeze as much speed out of all your computers as possible, because BitLocker encryption allows hardly over 800 passwords per second even if a top of the line NVIDIA card is employed. In other words, an 8-symbol alphanumeric password will take approximately 7,000 years to break by brute force with one GTX 1080 installed. Add four GTX 1080 boards, and you still have 1750 years to go. Scary? Not really. Years of our experience told us that passwords that have to be typed regularly tend to be easy to remember. So, checking a dictionary attack with mutations applied or wordlist with most popular passwords can get you your password.
Hopefully this article helped you decide which of the two tools you will need. If you still have questions unanswered, feel free to ask them right here in comments and we’ll get back to you with more details.