Every once in a while, hi-tech companies release reports on government requests that they received and served (or not). The different companies receive a different number of requests. They don’t treat them the same way, and they don’t report them the same way, which makes the comparison difficult. In this article, we’ll try to analyze and compare government request reports published by Apple, Google and Microsoft.
Since all three companies report on different things, and the sheer number of data is way too big for analyzing in a blog article, we’ll try to only compare data related to the North American region and Germany (as a single European country).
Apple
Apple is in a unique position. The company publicly and officially rejects all kinds of government requests to unlock its hardware (iPhone, iPod Touch and iPad devices running iOS 8 and newer). However, the company does reveal information about its user identities (based on Apple ID), and provides information stored on Apple servers such as iCloud backups, iCloud photos, iCloud Drive files as well as any information that is synced across iOS devices such as phone calls, text messages (SMS and iMessages), contacts, calendar events and email messages.
For government information requests, we report as much detail as we are legally allowed. When we receive an account request from law enforcement requesting a customer’s personal information, we will notify the customer a request concerning their personal data was made unless we are explicitly prohibited from doing so. We are reserving the right to make exceptions, such as for extreme situations when we believe disclosing information could put a child or other person in serious danger, or where notice is not applicable to the underlying facts of the case. Source: http://www.apple.com/privacy/transparency-reports/
In its report, Apple breaks down information requests into several categories.
Device Requests usually originate from law enforcement agencies working on behalf of customers locating lost or stolen devices. This category also includes multi-device requests related to fraud investigations. Requests to reveal customers’ identity based on device IMEI or other hardware identifiers are also included in this category.
During the reporting period of January 1 – June 30, 2016, Apple received 4825 device requests regarding 10263 devices in the North American region. Apple provided some data for 78% of those requests. Interestingly, the numbers differ greatly across regions. For example, in Germany the company received 12633 requests regarding 52095 devices, of which only 53% were satisfied. Russia submitted 126 requests about 425 devices, of which 44% were satisfied.
Notably, Apple does not include data on physical devices sent to the company for unlocking and extracting. The company’s official Privacy Policy states that Apple itself is unable to extract any data from locked devices running iOS 8 and newer (but might keep doing it for the occasional device still on iOS 7 or older). It is possible that this is the reason for Device Requests data to not contain information about physical extraction.
Account Requests may involve information about the user’s identity based on the iTunes or iCloud account ID, such as a name and an address. In addition, this category includes requests for iCloud content such as photos, email, iOS device backups, documents, contacts, calendars, and bookmarks.
During the reporting period of January 1 – June 30, 2016, Apple received 1365 account requests regarding 9092 accounts in the North American region. Apple provided some data for 84% of those requests. In Germany the company received 203 requests regarding 244 accounts, of which 52% were satisfied.
Interestingly, Germany submitted significantly more device requests compared to the US and Canada (52095 devices in Germany vs. 10263 devices in North America), while the number of account requests is dramatically smaller (information was requested for 244 accounts in Germany vs. 9092 accounts in North America). Based on these numbers, we can only speculate that iPhone theft is on a much higher level in Germany compared to North America, while local legislations are probably stopping German authorities from requesting account information from Apple.
National Security Orders include all orders received under FISA and National Security Letters (“NSLs”). Due to legal restrictions, Apple is only able to provide information about these requests in bands of 250.
During the period of January 1 – June 30, 2016, Apple received between 2000 to 2249 NSO requests, and that’s all we know about this category.
According to Apple, only a tiny fraction (0.00612%) of its customers were affected by information requests. Worldwide, some 94% of all requests were Device Requests, while only 6 % were Account Requests. National Security Requests were a tiny fraction.
More information:
Information Disclosed by Apple
According to Apple Law Enforcement Guidelines, the company may disclose the following information when processing Account Requests:
- Device Registration (customer’s name, address, email address, and telephone number)
- Customer Service Records (contacts that customers have had with Apple customer service; information regarding the device, warranty, and repair)
- iTunes (basic subscriber information such as name, physical address, email address, and telephone number; information regarding iTunes purchase/download transactions and connections, update/re-download connections, and iTunes Match connections)
- Apple Retail Store Transactions (cash, credit/debit card, or gift card transactions that occur at an Apple Retail Store)
- Apple Online Store Purchase (name, shipping address, telephone number, email address, product purchased, purchase amount, and IP address of the purchase)
- iTunes Gift Cards (information regarding the customer who redeemed the cards and transactional information about iTunes purchases)
- iCloud
- Subscriber Information
- Mail Logs
- Email Content
- Other iCloud Content (Photo Stream, Docs, Contacts, Calendars, Bookmarks, iOS Device Backups). iOS device backups may include photos and videos in the users’ camera roll, device settings, app data, iMessage, SMS, and MMS messages and voicemail.
- Find My Phone
In addition to this disclosure, we discovered that Apple retains (and may, in certain cases, disclose to law enforcement agencies) some other data. In addition to periodic cloud backups, Apple syncs certain types of data across iOS devices via iCloud. As an example, iPhones send information about phone calls and FaceTime conversations to iCloud just minutes after the call. Unlike iCloud backups, syncing occurs with or without Wi-Fi connectivity and whether or not the device is connected to a charger. In other words, the data will be synced on the go using available connectivity (including mobile data). iOS syncs call logs, Safari browsing history, notes, calendars and contacts.
- Synced call logs. Information about phone calls, FaceTime conversations and some other VoIP calls is saved as part of the call log, and synced with Apple servers with little or no delay. This is separate from iOS backups. Information about calls is synced with Apple servers just moments after the call.
- Safari browsing history. Again, this is synced across devices through iCloud.
- Notes, calendars, contacts.
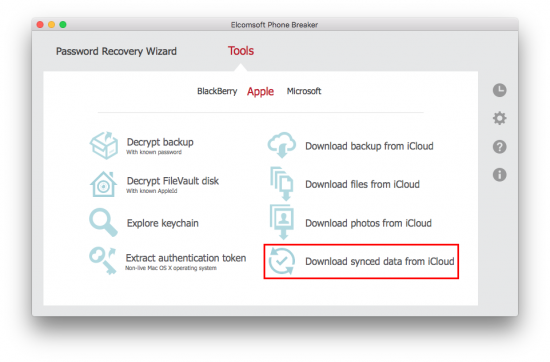
Extracting iCloud backups and synced data (as well as other data, such as documents and third-party application data, and of course media files) is possible with the latest version of Elcomsoft Phone Breaker. The following screenshot outlines the ability to extract synced data from Apple iCloud:
Download Elcomsoft Phone Breaker
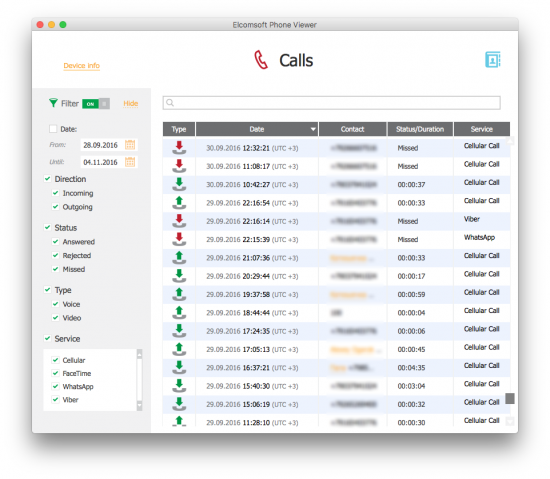
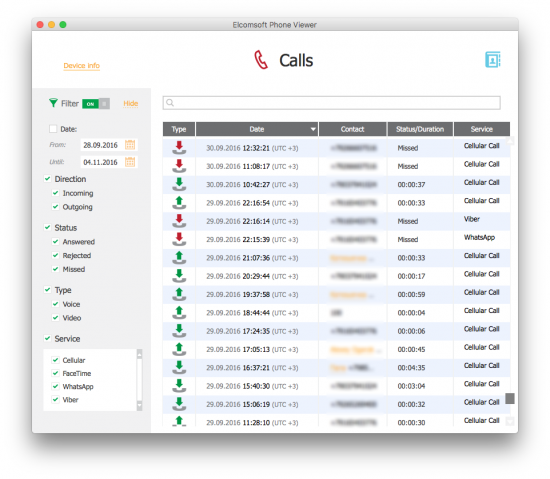
The data can be viewed with Elcomsoft Phone Viewer:
Finally, evidence exists that Apple breaks its promise (“your iMessage conversations are safe and out of reach from anyone other than you and your friends”) and retains metadata about iMessage contacts. This is how it looks on the law enforcement side. At very least, Apple logs contacts’ phone numbers and IP addresses if not the actual iMessage content. (On a side note, iMessages can still be synced via Continuity, which is a yet another protocol that may carry your data through Apple servers).
More information:
Google
In its Transparency Reports, Google details data requests originating from government entities. According to these Reports, the company received some 44943 User Data Requests during the first half of 2016, while 76713 requests were received for User Data. On average, Google complied with 63% of those requests. Let’s look into this in more detail.
The United States submitted 14168 User Data Requests covering 30123 accounts. 79% of those requests were satisfied. Germany served 8788 requests about 13425 accounts, of which 59% were satisfied. During the same period, Apple received 1365 account requests about 9092 accounts (North America) with 84% satisfaction rate, while Germany served Apple with 203 requests about 244 accounts (52% satisfied). The numbers appear to roughly correspond with the number of Apple/Google users: in June 2016, the US had 65.5% of Android users vs. 31.8% iOS users, while Germany was 80.3% Android vs. 16.5% iOS.
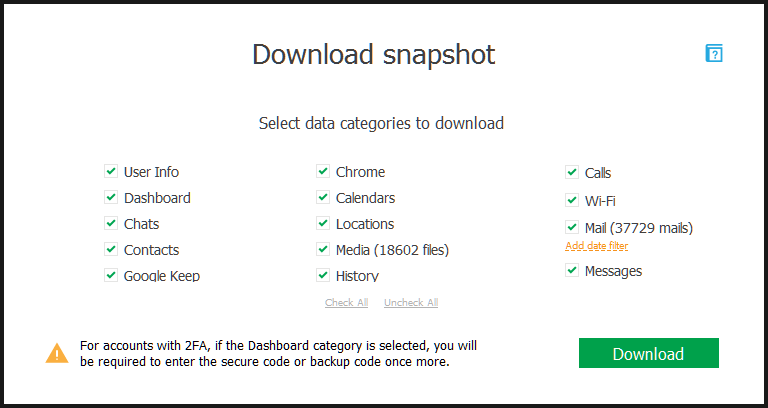
Note that Google does not detail the types of information provided to the law enforcement. This could have something to do with the company not willing to disclose what information is being collected beside the well-known types. In our product, Elcomsoft Cloud Explorer, we were able to extract the following information from Google:
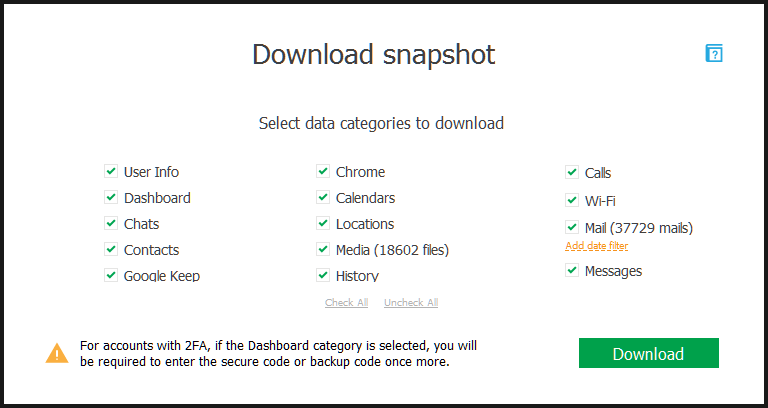
- User Profile and other info
- Messages (Google Hangouts)
- Call logs (Android 7.0 Nougat)
- Saved Wi-Fi credentials (SSID and passwords)
- Email messages (Gmail) via Gmail API
- Contacts (including synced contacts from mobile devices)
- Notes (Google Keep)
- Search History (including Web sites visited after firing up the search)
- Google Chrome data (synced bookmarks, Web forms, logins and passwords, page transitions)
- Media (images from Google Photos including EXIF data)
- Calendars
- Dashboard
- Location history
Download Elcomsoft Cloud Explorer
More information:
Microsoft
According to Microsoft Transparency Report, the company received a total number of 35,572 legal requests for customer information from law enforcement agencies in the first half of 2016. The company mentioned that just over 2.5 percent of law enforcement requests resulted in the disclosure of content customers created, shared or stored on Microsoft’s services. However, this number of 2.5% is misleading and may not correctly reflect the actual picture.
According to Microsoft, the United States law enforcement agencies submitted 167 requests regarding 172 user accounts in the first half or 2016. In 8.38% of cases, Microsoft has disclosed the actual content, while in 37.13% of cases only subscriber/transactional data was disclosed. Of requests that weren’t satisfied, in 48.50% the data was not found, while only 5.99% of cases were rejected. This does not look anywhere close to the 2.5% Microsoft cites for disclosing user content.
In Germany, Microsoft received 16 requests about 12 user accounts. The company did not disclose any user content, but in 62.5% of cases it disclosed user/transactional information. No data was found in 31.25% of cases.
As we can see, Microsoft received very few government requests compared to Apple and Google. While this actually corresponds with the company’s low mobile market share, it is genuinely surprising to see how few requests are submitted for BitLocker encryption keys (stored in Microsoft OneDrive) or Microsoft Account data containing users’ synced passwords, browsing history, OneDrive photos and office documents.
Just like Google, Microsoft does not provide detailed breakdown on what data, exactly, the company collects and discloses. Yet it is well-known that Microsoft’s latest desktop OS, Windows 10, collects astonishing amounts of information about its users. Moreover, with recent (over a year old actually) updates, Windows 7 and 8.x also collect information for Microsoft.
More information:
Analysis and Conclusion
The data provided by the three companies is difficult to compare due to the differences in what they choose to publish. In particular, Microsoft distinguishes account requests that resulted in the company providing only subscriber/transactional data; providing user-created data; failing to provide data due to non-existing account; and finally, rejecting the request. For the United States, about 37% of requests only revealed subscriber identities, while actual data was provided in about 8% of cases. No data was found in 48% of cases, and only 6% of cases were rejected.
Neither Apple nor Google provide such a detailed outline. Would it be reasonable to expect similar rates regarding the data that wasn’t found (due to a wrong account ID, deleted account etc.)?
Apple tells us that it provided “some” data in about 84% of all cases. In the North American region, this breaks down as follows: non-content data was disclosed in 8.23% of cases; some content was disclosed in 4.32% of cases; unspecified “data” was disclosed in 87.58% of cases, which may also include information about missing data. Apple objected to government requests in 1.47% of cases.
Google also quotes a number of 79%, which is the number of account requests in which the company has revealed some information. What kinds of information were revealed is unspecified. Could it be reasonable to expect a similar breakdown to the numbers posted by Apple or Microsoft? We don’t know.
Another thing we found is how many device requests Apple received in Germany (12633 requests regarding 52095 devices) vs. the number of account requests (203 requests regarding 244 accounts). This does not correspond with the numbers we see in the US and Canada, which submitted 1365 account requests about 9092 accounts and 4825 device requests about 10263 devices. These numbers just don’t play along. So much so that we decided to make a small table:
| |
Device requests / devices |
Account requests / accounts |
Regional iOS market share |
| North America |
4825 / 10263 |
1365 / 9092 |
31.8% |
| Germany |
12633 / 52095 |
203 / 244 |
16.5% |
Considering that device requests often originate from the law enforcement attempting to locate a lost or stolen device, it may appear that Germany has a dramatically higher number of iPhone theft. A rough estimate (statistica.com), Germany has about 50 million smartphone users (June 2016), 8.25 million of which are iPhones. With 52095 device requests, this could mean that one of 158 iPhones was reported stolen in the first half of 2016.
The US has about 200 million smartphone users, 63,6 million of which are iPhone users. If 10263 devices were reported lost or stolen, this could mean that every one of 6200 devices was reported to the police, a number nearly 40 times smaller compared to that in Germany. Whether these numbers correspond to reality is a big speculation based entirely on the number of device requests published by Apple.