Believe me or not, but this is exactly the 500th post in our blog! The first one was posted in March 2009 and was about Distributed Password Recovery and GPU acceleration. At that time, we even did not do mobile or cloud forensics. Today it’s not about our achievements. I want to thank you for being with us, and share a few bits and pieces about our blog that you may find handy or at least amusing.
We started our blog more than ten years ago. We never planned to be a pure marketing instrument. Instead, we tried our best to serve our readers with information that is rarely published and never mentioned in the marketing materials or even user manuals. Tips & tricks, step by step instructions, our view on some security and forensic news and challenges, results of our research and much more.
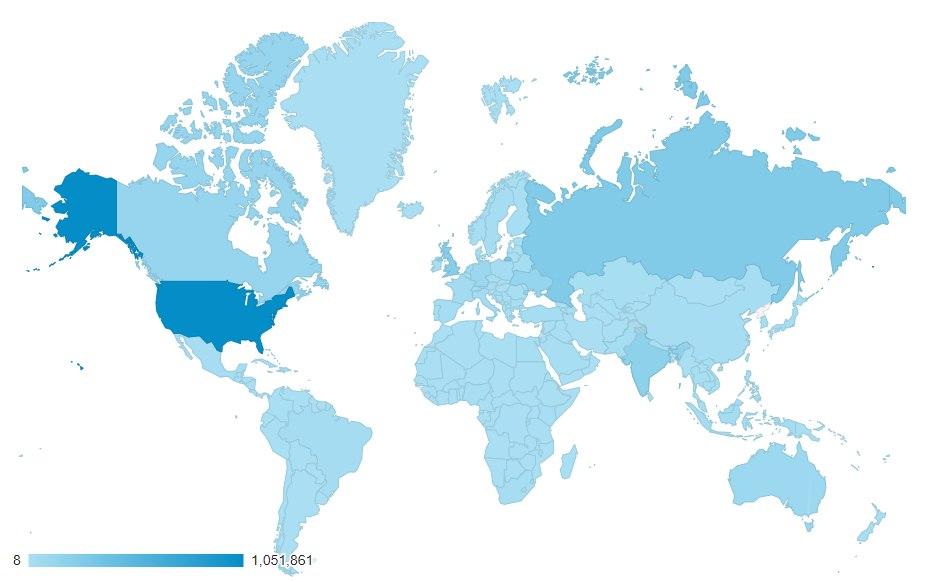
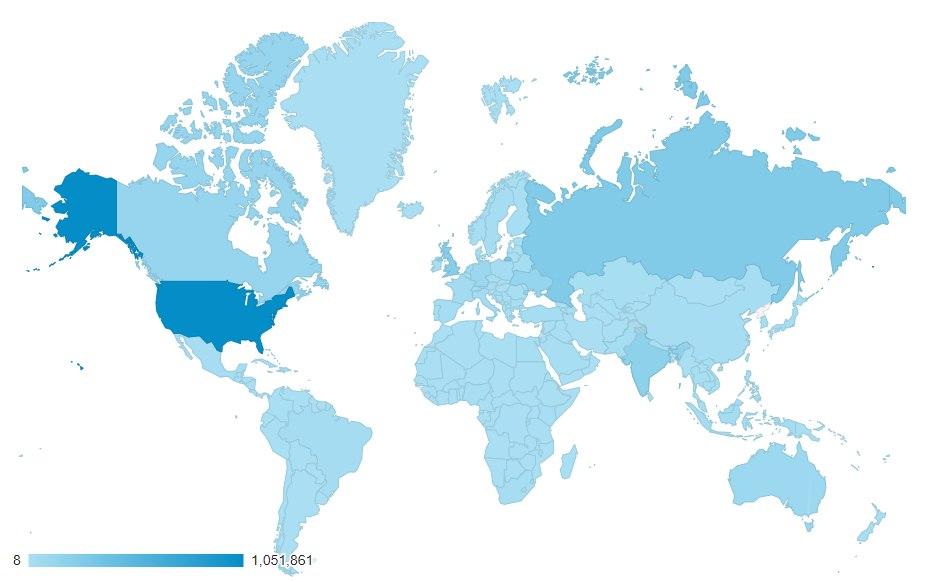
We have readers from all over the world:
In case if you are curious, here are our most popular articles:
Our blog is not the only reputable source of information for the forensic crowd. I want to share some free tools and resources you must have in your iOS forensic arsenal.
Jailbreaks
I don’t think I need to tell you about it, but checkra1n, which is a bootrom-level jailbreak for many iPhone models ranging from the iPhone 5s to the iPhone X, is a must for a mobile forensic expert. The jailbreak supports iOS 12.3 through iOS 13.7, and even iOS 14 for the iPhone 6 and iPhone SE.
In mobile forensics, jailbreaks are routinely used to perform file system extractions. If you don’t caret about the authenticity and repeatability of the process, you can even do it without any kind of forensic tools, just with ssh and tar. You won’t get the keychain this way, but it still might be an option.
Newer iPhones such as the iPhone Xr, iPhone Xs or iPhone 11, require a different jailbreak. unc0ver comes with iOS 11.0 to 13.5 support for all models except the iPhone 12 range, as it can only run iOS 14. We also recommend enrolling into the Apple Developer’s Program, which makes it far easier and far safer to install this and many other OS-based jailbreaks.
Binary tools
Over the years, we collected a number of tools we are using on a daily basis. I’d like to share the shortlist of free software you cannot live without. The list includes tools for working with plist files including binary ones, SQLite databases, iOS downgrades and even extended logical acquisition:
Scripts
There are many more free tools for specific purposes. Most of them are distributed as platform-independent scripts to help perform in-depth analysis and reporting of iOS logical and file system acquisitions.
Information
As I mentioned in the beginning of this post, our blog is not the only source of valuable information for the mobile forensic specialist. Apart from our own blog, there is a few excellent sources you may want to subscribe to:
Conclusion
Whether your budget is limited or not, free tools add a great value to your forensic software arsenal. The tools and scripts listed above can do quite a lot of things that even commercial software cannot. With some of them, you can literally extract and analyze a device without spending a dollar.
By the way, we are about to release another free tool for the forensic community soon. Stay tuned!