The past two years have become a turning point in iOS acquisition. The release of a bootrom-based exploit and the corresponding jailbreak made BFU acquisition possible on multiple devices regardless of security patches. Another exploit covers the entire iOS 13 range on all devices regardless of their hardware revision. ElcomSoft developed a jailbreak-free extraction method for the entire iOS 9.0-13.7 range. Let’s see what low-level acquisition options are available today, and when to use what.
The bootrom exploit
checkm8 (“checkmate”) is a permanent, unpatchable bootrom exploit for a wide range of Apple hardware installed in millions (if not hundreds of millions) of devices. Affected devices include the iPhone 5s, 6, 6S, SE, 7, 8, the iPhone X, as well as the “Plus” versions of the phones above. In addition, checkm8 is available for other devices based on the same platform. If you are not sure about the meaning of “similar platform”, check out Apple Mobile Devices Cheat Sheet.
checkm8 takes advantage of a vulnerability in the bootrom code on iOS devices, allowing users to gain root access to their iOS device. However, the exploit itself cannot be used easily by the public since it’s missing core components that are commonly included in public jailbreaks. Based on this exploit, the jailbreaking community had developed an all-in-one jailbreak, the checkra1n.
The checkra1n jailbreak has properties never seen in a jailbreak before. First, it’s (mostly) unpatchable: since the bootrom code is hardcoded, it cannot be modified by Apple, and the exploit cannot be fixed with the exception of the iPhone 8/8 Plus/X range running iOS 14.
Use the checkra1n jailbreak in the following cases:
- BFU extraction if the device is locked and the passcode is unknown
- iOS 14 on iPhone 6s, SE, 7, 8, and iPhone X; note that you’ll have to remove the passcode on the iPhone 8/X devices (passcode must be known)
The Odyssey jailbreak
Odyssey is an open-source jailbreak covering all iOS versions from iOS 13.0-13.7, including A12 & A13 devices (the iPhone Xr, Xs, Xs Max, iPhone SE 2, 11, 11 Pro and 11 Pro Max range). The installation may take several tries with reboots between them; the same applies to the extraction agent due to the nature of the underlying exploit.
We don’t recommend using Odyssey in the forensic extraction workflow. iOS Forensic Toolkit offers agent-based extraction, which delivers identical results with significantly smaller footprint and without the risks associated with jailbreaking.
Use Odyssey in the following cases:
- Not recommended
- Use agent-based extraction in iOS Forensic Toolkit 6.60 and newer
Other jailbreaks
Other jailbreaks (e.g. unc0ver) also exist, covering almost the entire range of iOS versions. We are expecting unc0ver to be updated with iOS 13.7 support. Does it make sense using any of the “other” jailbreaks? We don’t recommend using jailbreaks for iOS extraction if you want your workflow to remain forensically sound, but you may have no other choice. Agent-based extraction delivers identical results with zero risk and significantly smaller footprint.
Installing jailbreaks typically requires the use of a Developer account or one of the following:
- Online installation signed with a leaked enterprise certificate
- Via AltDeploy
- Via nullximpactor
- Via Xcode + iOS App Signer
Use other jailbreaks in the following cases:
- Use for iOS versions older than 9.0 (e.g. the iPhone 5s running iOS 7 and 8, iPhone 6 running iOS 8)
- Use agent-based extraction in iOS Forensic Toolkit 6.60 and newer for iOS 9.0 through 13.7
The Agent
When it comes to file system extraction and keychain decryption, we used to rely solely on publicly available jailbreaks. We were never happy with this approach as using jailbreaks is far from being forensically sound, while correctly installing some jailbreak requires significant efforts.
Therefore, in the beginning of 2020, we started developing a different method for low-level acquisition. In March 2020, the new method was officially released. This all-in-one extraction method utilizes an extraction agent of our own development. The extraction agent integrates known exploits to escalate privileges, gain access to the file and the encryption keys required to decrypt the content of the keychain. Agent-based extraction provides numerous benefits over jailbreak-based acquisition, being a lot safer, a lot faster, and a lot more robust.
Today, the extraction agent supports the entire range of iOS releases from iOS 9.0 all the way through iOS 13.7 with no gaps or exclusions, for all generations of Apple hardware capable of running these versions of iOS.
The extraction agent requires using an Apple Developer account (why?), yet macOS users can use a regular Apple ID.
We recommend using the iOS Forensic Toolkit extraction agent for all extractions if the device runs a compatible version of iOS and you know the screen lock password.
Use iOS Forensic Toolkit extraction agent in the following cases:
- For all devices running iOS 9.0 through 13.7
- Apple Developer Account required (Windows) / recommended (macOS)
- Screen lock password must be known or empty
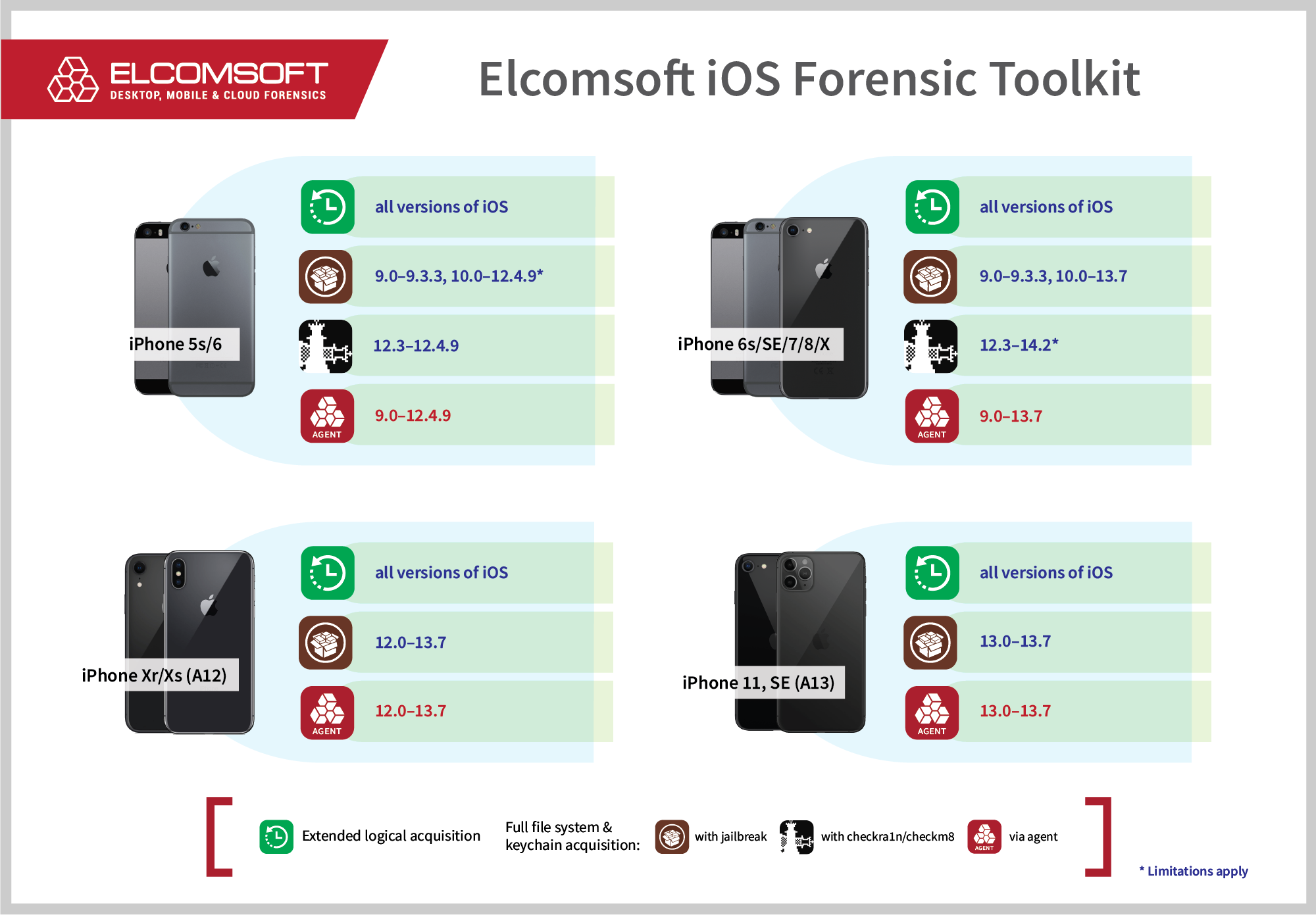
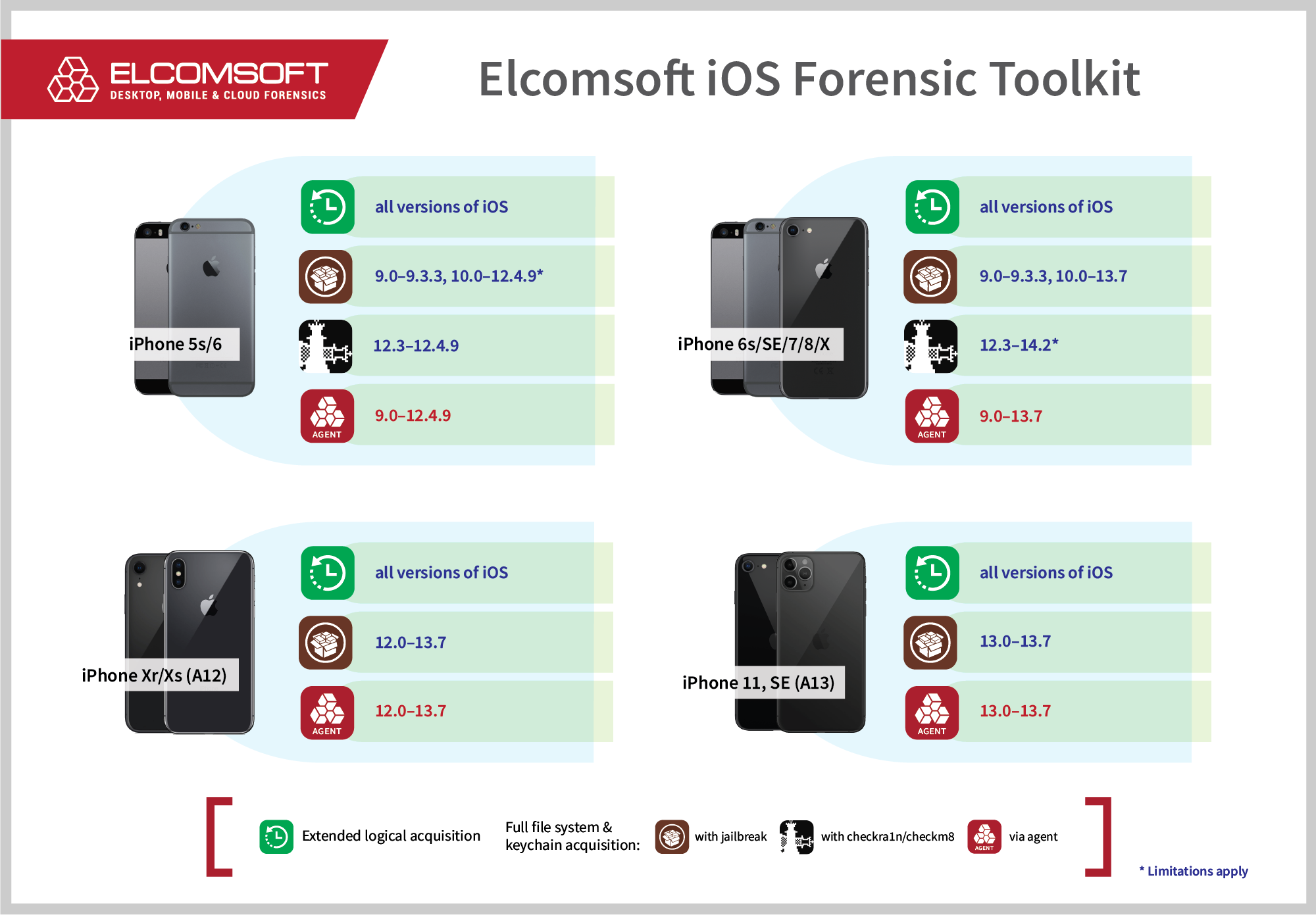
Here’s the updated chart of supported platforms:
We have successfully tested the new version of the extraction agent on all of the following devices:
- iPhone 7: iOS 13.5.1, iOS 13.6, 13.7
- iPhone X, iOS 13.7
- iPhone Xr, iOS 13.6.1
- iPad Pro 3rd gen, iOS 13.7