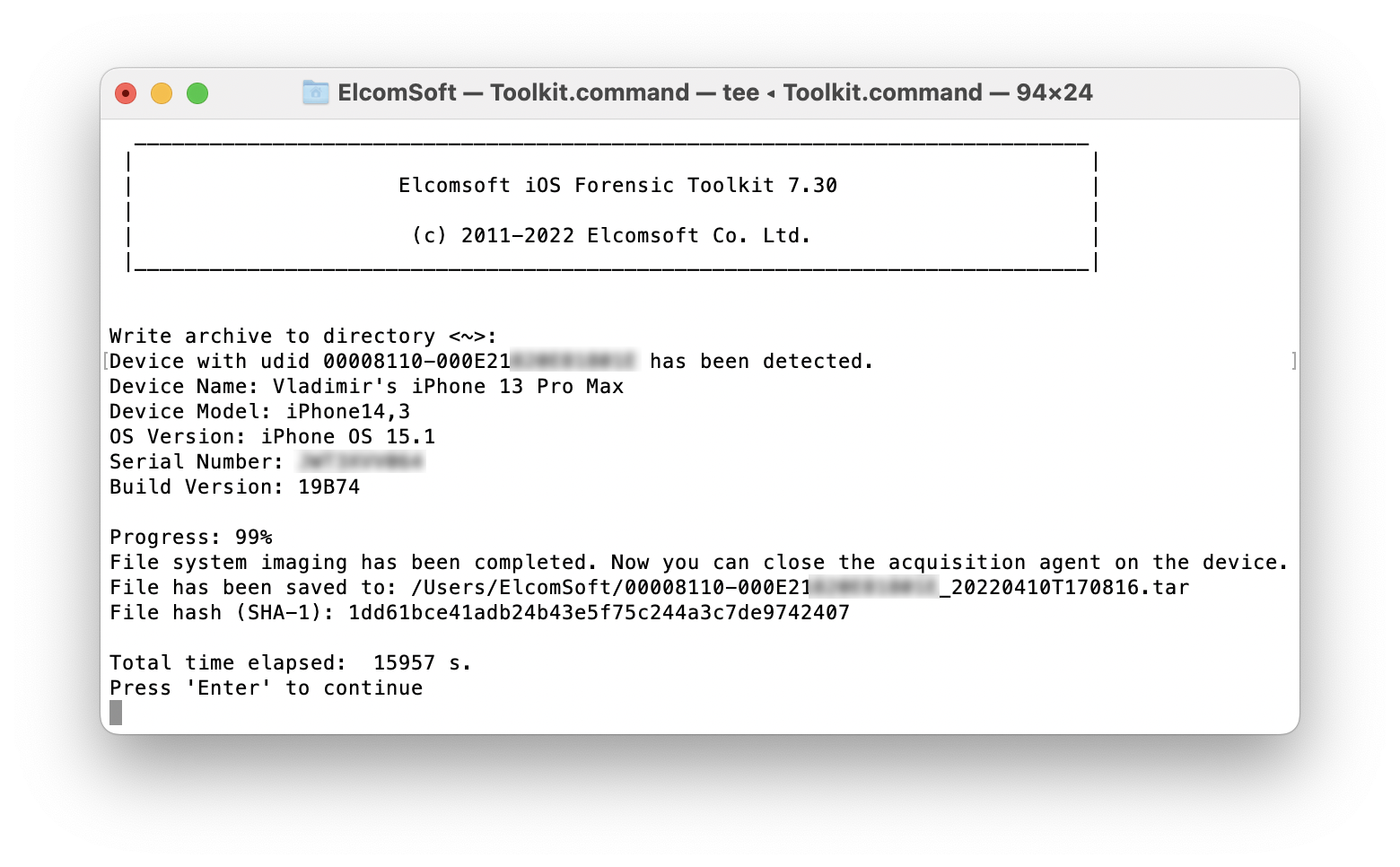
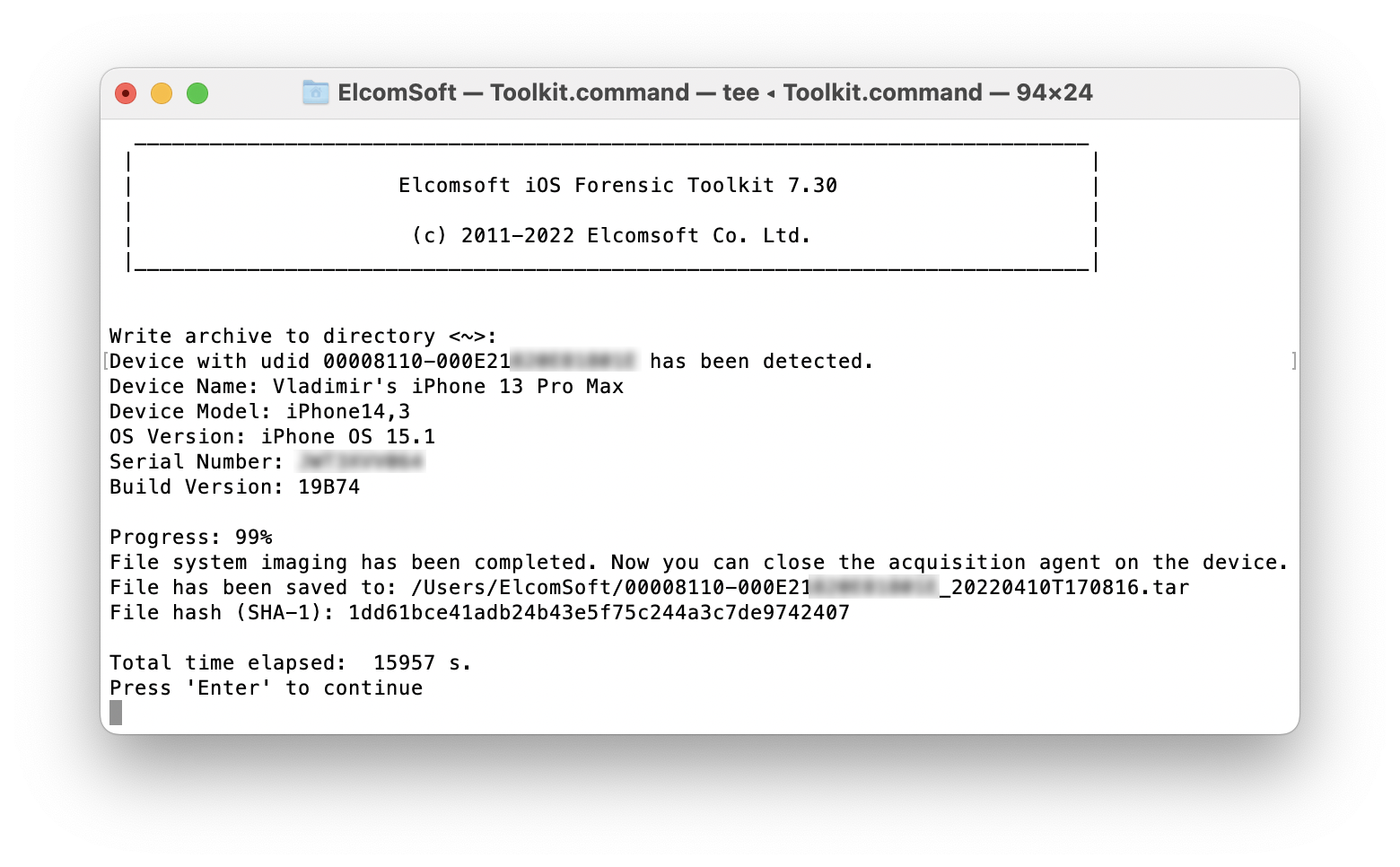
While we continue working on the major update to iOS Forensic Toolkit with forensically sound checkm8 extraction, we keep updating the current release branch. iOS Forensic Toolkit 7.30 brings low-level file system extraction support for iOS 15.1, expanding the ability to perform full file system extraction on iOS devices ranging from the iPhone 8 through iPhone 13 Pro Max.
Agent-based file system extraction
There are several extraction methods of varying quality and applicability starting with logical acquisition. Low-level is vastly superior to logical extraction, offering a significantly larger set of data and generally cleaner extraction process. Low-level extractions can be implemented in a few different ways. For older devices, the checkm8 extraction delivers the best results; our solution is unrivaled in providing truly forensically sound results. At this time, the checkm8 extraction process is still in beta (although you are welcome to test iOS Forensic Toolkit 8.0, which was just updated to beta 6).
Notably, checkm8 only works with older iPhones; it is simply not applicable to newer devices. To deliver low-level extraction for the rest of Apple hardware, we developed an in-house extraction agent that comes as close to being forensically sound as possible. This method is highly dependent on kernel exploits, which are extremely difficult to implement. This is why low-level extraction almost never comes to the current, up-to-date and fully patched versions of iOS. For newer models starting with iPhone Xr/Xs, using the extraction agent is the only way to access the file system.
What is the extraction agent?
When extracting an iOS device, we still need low-level access to the device. For this, we developed our own solution based on the extraction agent, which is an app sideloaded to the iPhone. The extraction agent establishes a communication channel between the device and the computer, escalates privileges, and gains access to the file and the encryption keys required to decrypt the content of the keychain.
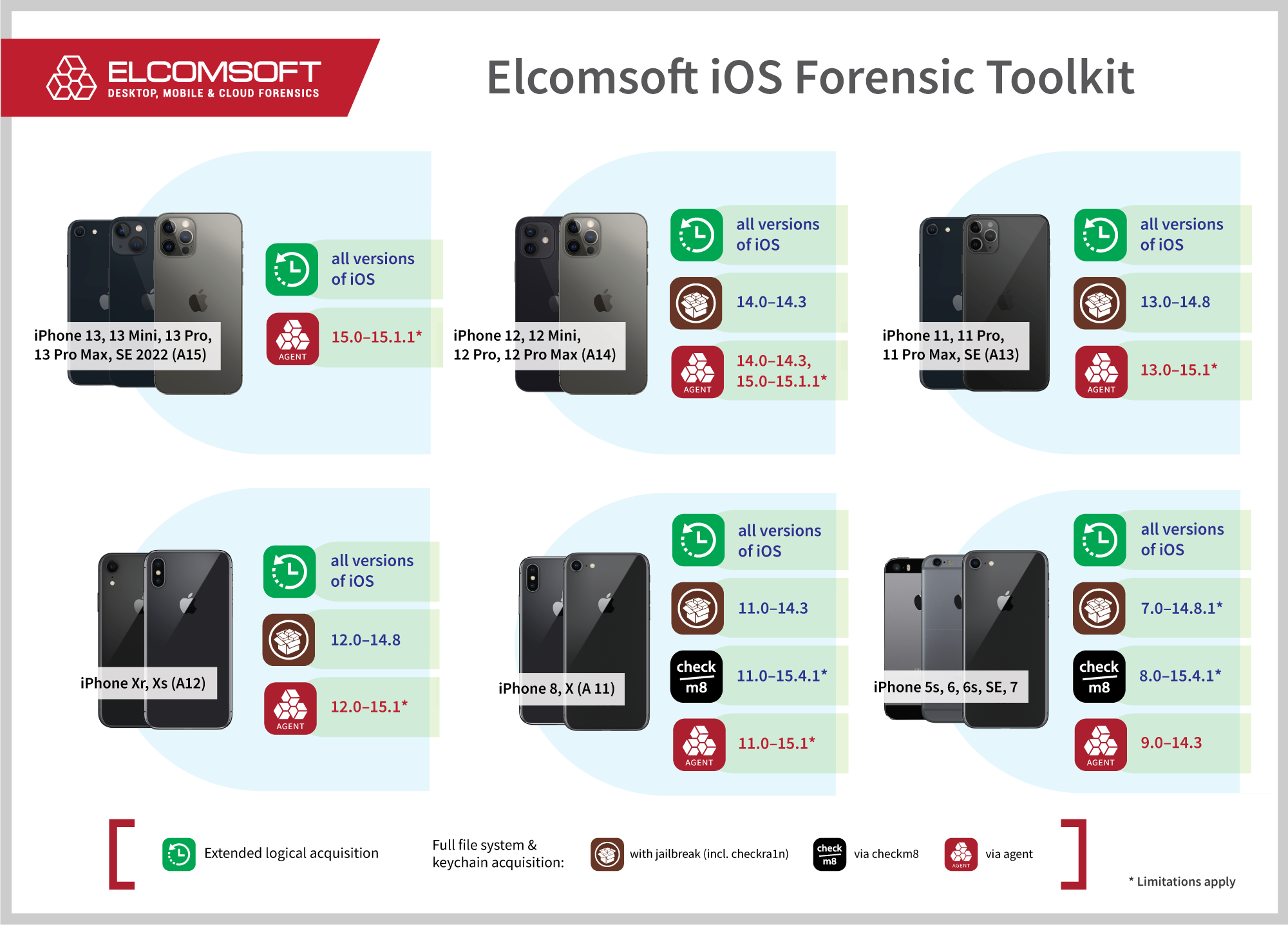
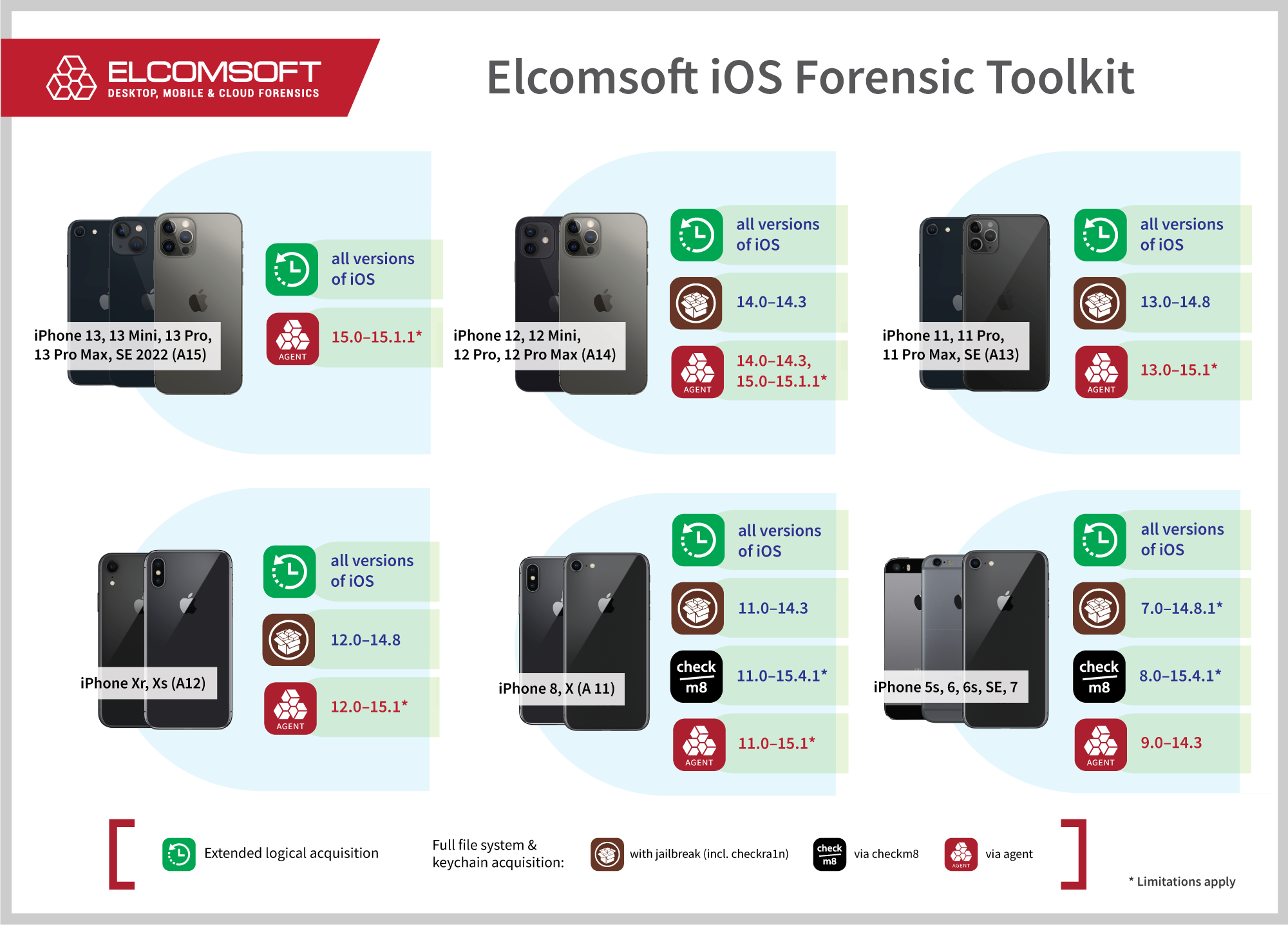
iOS Forensic Toolkit 7.30 adds support for iOS 15.1.1. This, however, does not result in gapless coverage. For example, we don’t currently have support for iPhone 12 devices running iOS versions 14.4 through 14.8, while iOS 14.8.1 is not supported at all. In addition, for A12-A15 devices we are only able to decrypt keychain items if the device is running iOS versions up to and including 14.4.2. We are working hard to overcome these limitations. Finally, we are working on iOS 15.2, which has an exploit available but is more complex to support.
Does all of that sound confusing? We’ve made a glanceable infographics to make the current compatibility matrix easier to grasp:
Using the extraction agent
You’ll need a supported iPhone or iPad device running a compatible version of iOS. Please refer to the above picture for the matrix of supported device models and iOS versions.
Using an Apple ID registered in Apple’s Developer Program is strongly recommended for installing the agent as it alleviates the need to open Internet access on the device. You can read more about installing the agent in iOS Low-Level Acquisition: How to Sideload the Extraction Agent.
Steps to extract the file system and decrypt the keychain
To extract the file system and decrypt the keychain from an iOS device without a jailbreak, follow these steps.
- Connect the iPhone to your computer. Pair the device (establish trusted relationship) by confirming the prompt on the iPhone and entering the screen lock passcode.
- Launch iOS Forensic Toolkit 7.30 or newer.
- On the computer, sideload the extraction agent by using the corresponding command in iOS Forensic Toolkit. Please refer to iOS Low-Level Acquisition: How to Sideload the Extraction Agent for instructions.
- On the iPhone, launch the extraction agent by tapping its icon.
- If supported, extract the keychain. The keychain can be extracted from supported devices and iOS versions (please check the compatibility matrix above).
- Extract file system image (full file system or data partition). We recommend extracting the data partition only; the full image may be usable e.g. to check the system partition for persistent malware.
- On the iPhone, uninstall the extraction agent in a regular way.
- You may now disconnect the iPhone and start analyzing the data.
Troubleshooting
If you encounter the “Cannot start installation proxy service on the device” error, disconnect and restart the iPhone. Reconnect it to the computer and re-establish pairing if necessary, then try again.