The iPhone Data Recovery Myth: What You Can and Cannot Recover
July 10th, 2020 by Oleg Afonin
Category: «Mobile»
There is no lack of tools claiming the ability to recover lost or deleted information from the iPhone. These tools’ claims range from “Recover data lost due to water damaged, broken, deletion, device loss, etc.” to the much more reserved “Selectively recovers iPhone data from internal memory, iCloud, and iTunes”. Do any of those tools actually work, and do they live up to the user’s expectations? The answer is complex, hence this article. Let us place the claims through our usual scrutiny.
The “water damaged” iPhone
When researching the various data iOS recovery tools, I was baffled by the very ambitious claim made by one data recovery company (you’ll easily find it if you look). The company makes a bold statement, claiming that its tool can “Recover data lost due to water damaged, broken, deletion, device loss, etc.” (original spelling preserved). Let’s first deal with the “water damaged” claim, as in “the device doesn’t power on”.
User expectations: The bold claim makes me think that the tool can somehow magically extract information from a sunk device that cannot be powered on.
Reality: This is not going to happen. While a specialized data recovery lab could try temporarily reviving the water-damaged iPhone for the time they need to copy your data off the device (and charge you an arm and a leg for just trying), no end-user software (and definitely no free software) can do that.
What the tool does: Interestingly, the claim is not necessarily a lie. It’s marketing. The data recovery tool can try downloading (thus “recovering”) information from your iCloud account. This may include backups (although we are yet to see a tool that can do that reliably, let alone free of charge) and some synchronized data (which may include your photos if you enabled the iCloud Photos setting in your iPhone). We have not seen any consumer-grade tool that can download your passwords or messages (SMS and iMessage history) because end-to-end encryption.
Limitations: “Downloading iCloud backups and photos” sounds good enough; let’s do that! While this may be possible (as in “you may be able to find a tool that actually works”), the problem is whether you have those backups at all. The many years of experience have taught me that the more valuable and unique data the user has, the less likely he or she will have a backup of that data. If you are reading this article, do check if you have a recent iCloud backup of your device, and if you have iCloud Photos enabled.
Since Apple only offers 5GB of iCloud space free of charge, most probably neither the backups nor photos will fit, so most likely you’ll end up with some very old backups and few, if any, photos. Paying for additional space in iCloud is one way to ensure your photos are backed up. Another is using a third-party cloud provider (e.g. Google Photos or Microsoft OneDrive) to back up your photos.
The right way: If all you need is your photos, and you had iCloud Photos enabled, you can download them easily to your computer without any third-party tools at all. For macOS, just connect your Apple account and use the Photos app. In Windows, Set up and use iCloud Photos on your Windows PC.
The “broken” iPhone
How the “broken” iPhone is different from “water damaged”? If the device cannot be powered on, there is no difference from the point of data recovery. However, the “broken” iPhone might have its display shattered and the touch functionality not working. If this is the case, you may be unable to unlock the device as you won’t be able to enter your passcode. Interestingly, in certain cases the data can be recovered from such devices.
User expectations: I plug the phone to the computer, and the tool connects through whatever magic protocol and pulls the data.
Reality: This may happen if you can unlock your iPhone (e.g. with Touch ID/Face ID) and the phone was previously “trusted” on your computer (a lockdown file/iTunes pairing record exists). Otherwise, you’ll have to enter the passcode on the device to establish trust relationship between the computer and the phone. Assuming that your touch screen is broken, you’re out of luck. Replacing the display might be your best recourse.
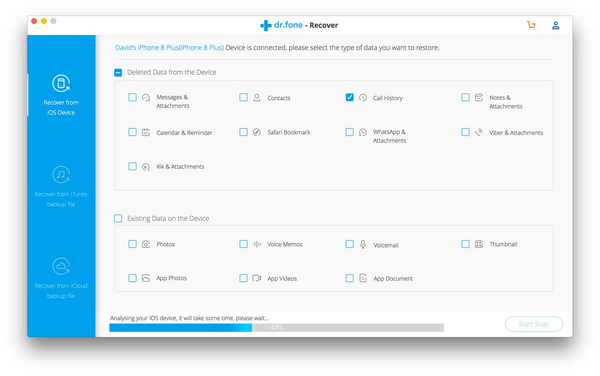
What the tool does: The tool will attempt to make a backup and/or pull your photos (that’s a different protocol that works even if your backups are password-protected). This is similar to the advanced logical acquisition process we do in Elcomsoft iOS Forensic Toolkit. Some of the more advanced data recovery tools may take advantage of existing pairing records/lockdown files, while others will not.
Limitations: You must had established a trusted relationship between your iPhone and your computer before it was broken. If there no trust exists, you’ll have to type the screen lock passcode on your iPhone to establish one, which may not be possible if the touch screen is broken.
The right way: If all you need is your photos, and if you had previously paired your iPhone with your computer, you can import them to your computer without third-party tools by following the instructions. Learn how to Import photos and videos from phone to PC. However, if you want to review your text messages/iMessages, or if you need some other information, you will need creating an iTunes-format first, and a tool to analyze that backup. Apple does not make tools for analyzing iTunes backups (only allowing you to restore the data to a new iPhone), so a third-party tool can help you. We are offering Elcomsoft Phone Viewer just for that purpose.
The “deleted data”
The “deleted data recovery” claim is the most ambiguous. While users expect the ability to recover deleted files of any kind, this is not the case. In the iPhone, almost every user file is stored encrypted. The file system employs file-based encryption with separate, unique encryption keys for every file. Once a file is deleted, the encryption key is momentarily destroyed, making it impossible to “undelete” or recover that file even if one had low-level access to the data partition (which, by the way, is not possible without a jailbreak or exploit).
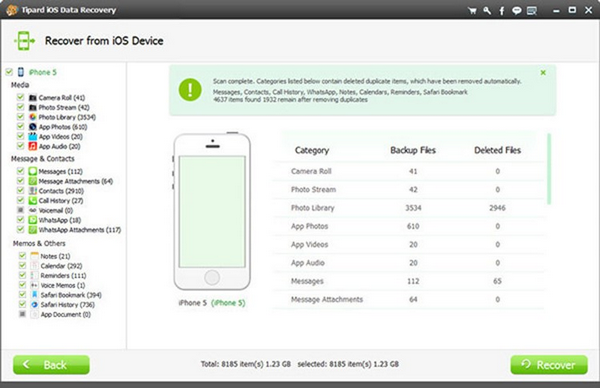
However, certain types of data can still be recovered – simply because they either aren’t files or aren’t really deleted. These types of data include:
Photos and videos. Once you delete a picture on the iPhone, the system does not actually delete the file. Instead, the image is moved to a special album (the “Recently Deleted” folder). Photos are kept in the Recently Deleted album for at least 30 days. During that period, users can easily restore their deleted pictures.
Messages. Your text messages and iMessages are stored in a database in the SQLite format. By default, SQLite does not overwrite records immediately after they’ve been deleted. Instead, SQLite marks them as “deleted”. Deleted pages become unused, and are stored on what is called a “freelist”. If you obtain the database files (by making a backup), these records can be recovered until the moment the database is fully vacuumed and defragmented (if it is, the deletion becomes permanent). This used to be the case in iOS 8 through iOS 11. Starting with iOS 12, Apple seemingly moved to a non-standard implementation, physically wiping records almost immediately after they are deleted. As a result, deleted text messages and iMessages cannot be recovered in iOS 12, 13 and newer.
Bookmarks. Deleted Safari bookmarks are stored in the HomeDomain/Library/Safari/Bookmarks.db database in SQLite format. Deleted bookmarks could be recovered from the SQLite database up to and including iOS 12. Starting with iOS 13, deleted bookmarks can no longer be recovered.
History. Safari browsing history is stored in the AppDomain-com.apple.mobilesafari/Library/Safari/History.db SQLite database. Starting with iOS 12, deleted Safari history can no longer be recovered.
Tabs. Starting with iOS 10, Safari open tabs are stored in the AppDomain-com.apple.mobilesafari/Library/Safari/BrowserState.db SQLite database. In iOS 10 and 11, open tabs would be stored indefinitely until closed, including tabs opened in the Private browsing sessions. However, even after the tabs have been closed, they could still be recovered. Starting with iOS 12, this is no longer the case. iOS 13 brings an additional protection mechanism, allowing users to specify the maximum period of time a tab can remain opened, automatically closing the tab and wiping the corresponding record after that period of time. In iOS 12 and 13, information about closed Safari tabs can no longer be recovered.
Reading List stores Bookmarks with com.apple.ReadingList as a parent. Items deleted from the Reading List can no longer be recovered since iOS 13.
Contacts, calendars, notes, and call history. All of these are also stored in their corresponding SQLite databases. Deleted records can be recovered by pulling and scanning the database files unless the database has been vacuumed and defragmented.
Files in the Files app. Files you store on your device in the Files app are moved to the Recently Deleted folder once you delete them. You can find and restore those files by opening the Locations > Recently Deleted folder.
Files in iCloud Drive. Just like the photos and videos, files you store in iCloud Drive aren’t immediately deleted. According to Apple, “When you delete a file from iCloud Drive, it goes into the Recently Deleted folder. If you change your mind or accidentally delete a file, you have 30 days to get it back. Go to Locations > Recently Deleted. Select the file that you want to keep and tap Recover. After 30 days, your files are removed from Recently Deleted.”
As you can see, most data can be only “recovered” (the proper term would be “restored”) from previously made backups – if you have ever made those backups anyway.
Below is a quick table to sum it all up. As you can see, starting with iOS 13 almost nothing can be recovered regardless of the type of backup you have (iTunes, iCloud, synchronized data or the TAR or ZIP file produced via file system imaging).

Deleted data, Part II
Okay, so we’ve got the grip of the “deleted” part. In older versions of iOS (and this is where most of the “iOS data recovery” tools grow their legs), anything stored in SQLite databases you might be able to recover given that the database had not been vacuumed and compacted. The only problem: it no longer works today. Some types of data became unrecoverable in iOS 12, while Apple started wiping the rest in iOS 13. Today, most iOS data recovery tools relying on SQLite freelists are useless.
Technically speaking, one could possibly access SQLite databases directly via a jailbreak or exploit. This is not going to be a one-button solution, far from it, and you will not gain access to most deleted records anyway. You’ll need a low-level forensic-grade extraction tool (e.g. Elcomsoft iOS Forensic Toolkit) and a tool like SQLite Forensic Toolkit to analyze write-ahead logs (WAL). Alternatively, forensic-grade software such as UFED or Oxygen can be used, neither of which is aimed at the home user.
Schrödinger’s backups
The one problem of recovering deleted records (be it messages, call logs or contacts) is the volatile nature of SQLite databases in modern versions of iOS. The only easy way to obtain SQLite databases from the device is making an iTunes backup. Until you make the backup, the databases are used with unmerged WAL (write-ahead logs), and some unmerged deleted records may still be recoverable. However, the very moment you initiate the backup, the SQLite databases are merged, and the deleted records are lost forever.
There is a single exception to this rule: the media files database one can obtain via the AFC protocol. These databases contain metadata for all indexed images and video files, including those the user deleted (and subsequently cleaned from the Recently Deleted album). However, there is very little value in image metadata for all but the forensic crowd.
Which leaves the “recovery” possibilities to restoring the data from an old (existing) backup. If you have a habit of making iTunes backups regularly… okay, nobody does, skip that.
If you have an existing iCloud backup containing the data that you’ve deleted after making the backup, you may be able to download that backup (we only know one tool that can and does, even if your account is protected with two-factor authentication; that’ Elcomsoft Phone Breaker). Note, however, that if you enabled “Messages in iCloud”, the messages will not be part of the iCloud backup anymore; instead, they’ll be synced with the cloud. “Messages in iCloud” are protected with end-to-end encryption; at this time, Elcomsoft Phone Breaker remains the only tool that can access end-to-end encrypted data in iCloud.
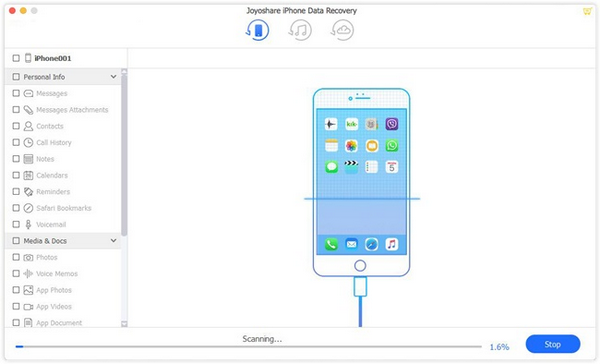
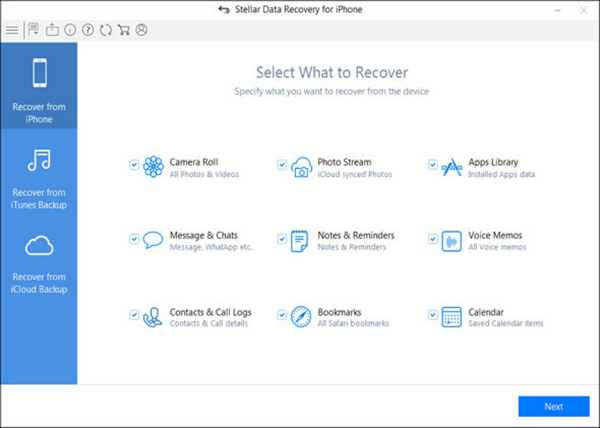
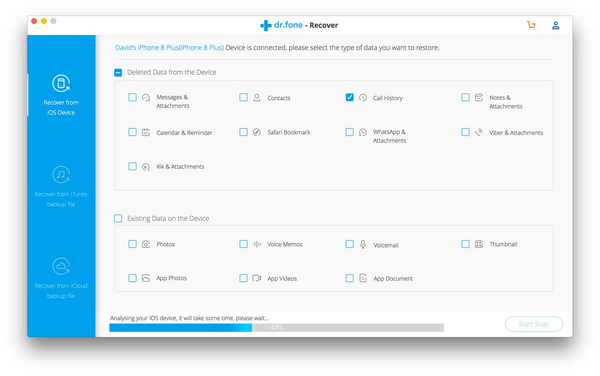
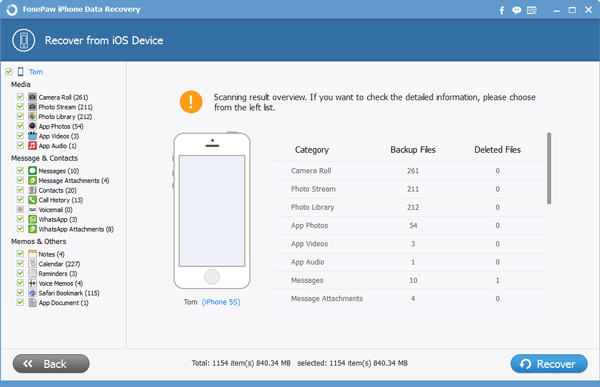
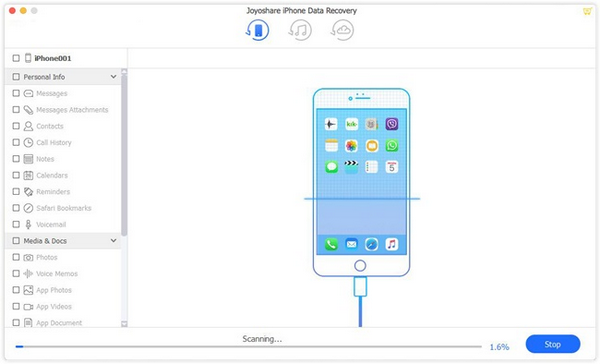
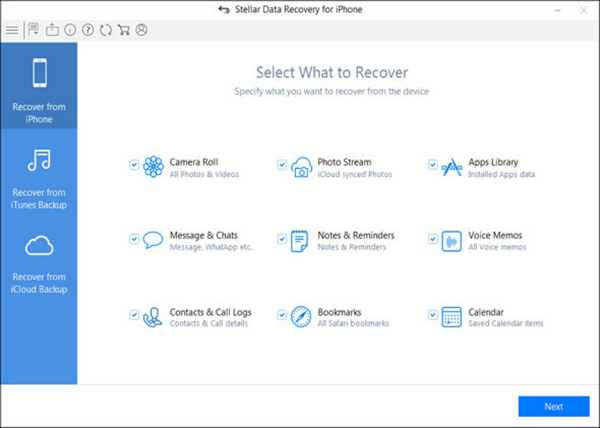
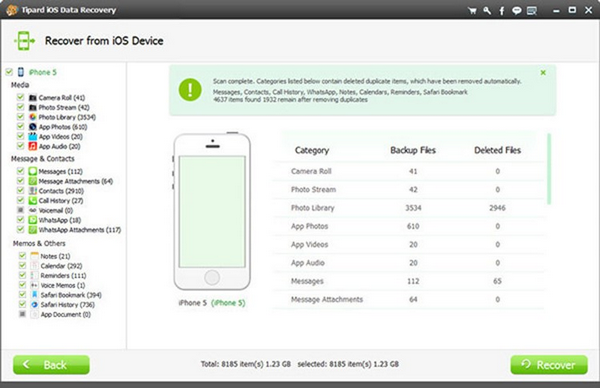
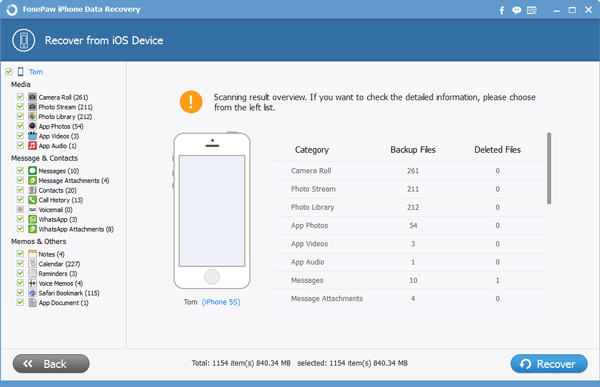
The clones
Just a quick note: the iOS recovery tools have become so popular that many of them are the same “white label” thing offered under a plethora of different labels. I would stay away of such tools as many of these so-called “manufacturers” will be unable to deliver the expected level of technical support should you need one.
Conclusion
With too many ambiguous claims, it is hard to trust the many iOS data recovery tools. Understanding the basic principles of their operation as well as the sources of the data used by such tools is important for adjusting one’s expectations. The absolute majority of data iOS recovery tools are based exclusively on the iOS/iTunes backup mechanism and the separate media synchronization protocol. Few tools can obtain synchronized information (such as the contacts, notes and calendars) from iCloud, and even fewer can download iCloud backups. We are yet to see an iOS data recovery tool that could pull an iCloud backup from a 2FA-protected account.