iOS Forensic Toolkit: Troubleshooting Low-Level Extraction Agent
September 12th, 2023 by Oleg Afonin
Category: «General»
In this tutorial, we will address common issues faced by users of the iOS Forensic Toolkit when installing and using the low-level extraction agent for accessing the file system and keychain on iOS devices. This troubleshooting guide is based on the valuable feedback and data received by our technical support team.
What kind of troubles are we shooting?
In this guide, we won’t dive into the inner workings of the extraction agent, which leverages known vulnerabilities to elevate privileges in Apple iOS. Instead, we’ll focus on what to do when you encounter a difficulty installing or using the extraction agent.
Common mistakes
First, let us cover the two most common mistakes our users regularly make when using the extraction agent.
- Attempting to Sideload the Agent Without a Firewall: If you try to install and run the extraction agent without using a firewall (software-based or the one using our Raspberry Pi or Orange Pi solution), you may expose the device to the risk of remote lock or wipe.
- Solution: Follow the installation instructions provided in the user’s manual. Understand how to configure and use a firewall to install the extraction agent without putting the data at risk.
- Alternative: Use an old Apple Developer account registered before 6 July 2021. In this case, you will not have to verify the signing certificate on the device.
- Extracting Only the File System Image Without Keychain: Only imaging the file system image without extracting the keychain is a common mistake.
- Solution: Always perform keychain extraction before imaging the file system. We recommend going after the keychain in the first place, which is nearly instant, followed by file system extraction, which may take a while.
Preparing the Device
Before you start sideloading and using the extraction agent, make sure to perform all of the following checks.
Compatibility check: iOS version
The extraction agent supports a wide range of iOS releases. Before you begin, get the exact version of iOS installed on the device, and check it against the iOS Forensic Toolkit compatibility list. Make sure that the version of iOS Forensic Toolkit you are using supports the version of iOS installed on the device.
Important: We are continually working on expanding the list of supported iOS versions for the extraction agent. You may find that your installed version of iOS Forensic Toolkit does not support a given iOS build, while a newer version does. If this is the case, you will need to update iOS Forensic Toolkit to the latest version.
Date and time on the target device
When launching the extraction agent, iOS checks if its digital signature is valid. If the device has been deeply discharged, its time and date settings may be way off, which will cause the verification to fail.
Solution: Set the correct date and time in the device’s settings. You may need to reinstall the extraction agent.
Check device pairing
Ensure that the target device is correctly paired to the computer. To do that, run the following two commands:
EIFT_cmd normal unpair
EIFT_cmd normal pair
Disable Internet sharing after signing the extraction agent
Do not forget to disable internet sharing after signing the agent app.
If you forget to disable internet sharing from your computer after signing the agent on the target device, there’s a risk of data loss due to receiving a command for remote locking or remote device wipe during operation.
Do not use VPN or proxy when signing the extraction agent
Signing the extraction may fail if the computer has an active VPN or proxy connection. Disable VPN and proxies when signing the extraction agent.
Use USB Type-C to Lightning cable
While checkm8 extraction usually requires a USB-A to Lightning cable, agent-based extraction works better with a certified USB Type-C to Lightning cable. We found that using Type-C to Lightning cables delivers extractions that are both faster and more reliable.
Errors Installing and Using EIFT
In this section, we’ll cover the common problems that may arise during the installation and usage of the extraction agent and iOS Forensic Toolkit.
“Insufficient Permissions” or “Not Found” errors
If you receive the “Insufficient Permissions” error when running iOS Forensic toolkit or the firewall script, this can mean that the tool had not been correctly installed on the computer. These problems can be broken down into the following cases.
The xattr command was not run correctly
To fix this issue, follow these steps:
- Open Terminal.
- Navigate to the folder containing containing iOS Forensic Toolkit.
- Execute the following command (mind the dot at the end of the command):
- sudo xattr -d com.apple.quarantine .
iOS Forensic Toolkit folder is located on the desktop
Solution: Move EIFT to a different location, such as the local Applications folder.
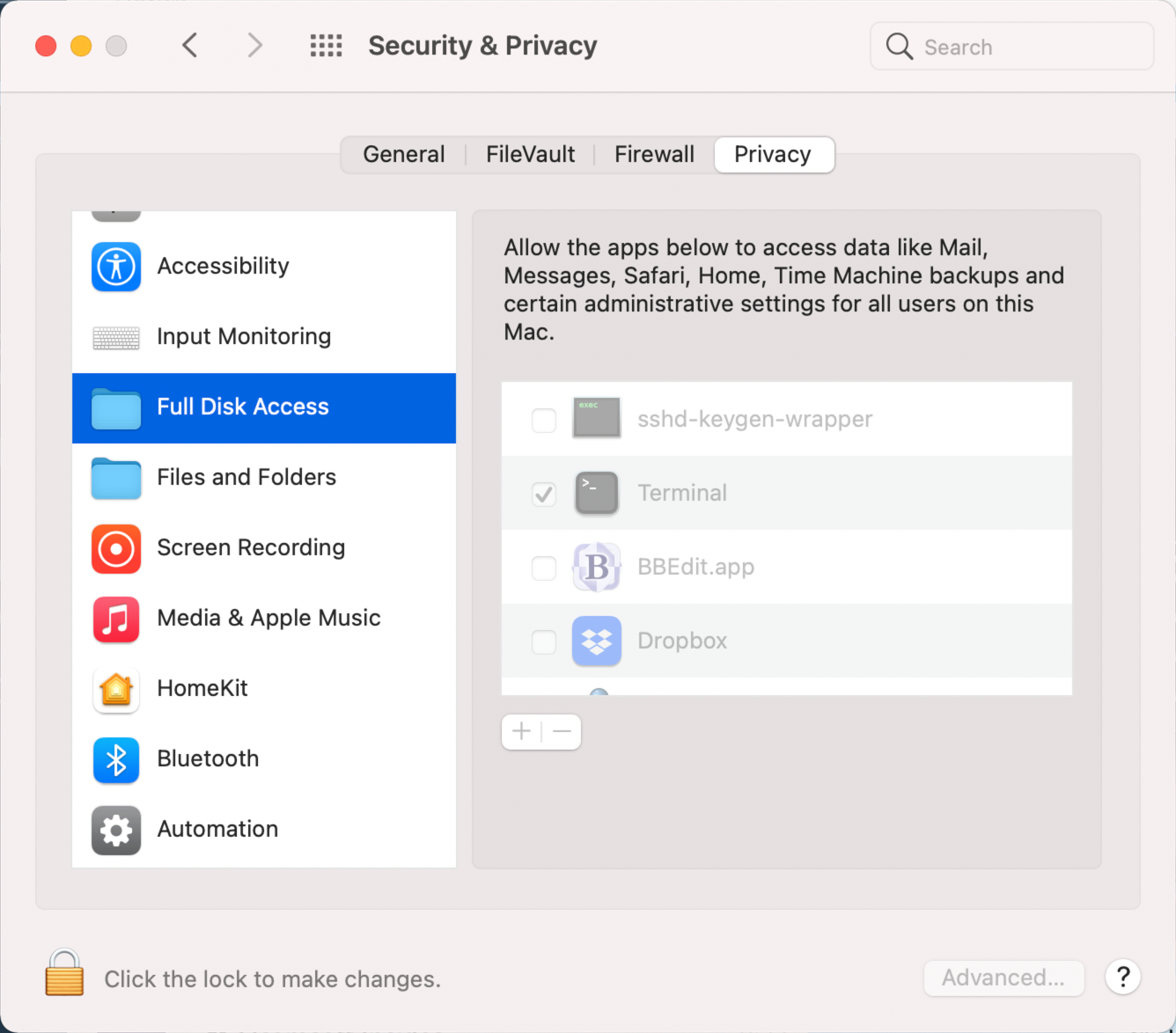
Shell does not have full disk access permissions
You must grant full access permissions to the OS shell.
- Go to System Preferences -> Security & Privacy -> Full Disk Access
- Click on the padlock icon to allow changes
- Click the ‘+’ button
- Press ‘cmd + Shift + .’ to display hidden files
- Select /bin/sh as a path
Misconfigured Internet sharing for USB devices
Typically, the problem arises from selecting the wrong internet source. Sometimes, more than one iPhone/iPad connection may appear in the list.
Solution: You need to manually identify the correct connection, often through trial and error, using a designated test device.
The firewall is running, tested OK, but sideloading does not work on the target device
- MDM profile on the device disallows sideloading
- Solution: do risk assessment and either remove MDM profile (risking to lose some types of data) or use a different extraction type (e.g. advanced logical)
The firewall is running, tested OK, but signing does not work on the target device
- Incorrect date and time on the target device
- Solution: check and set current time and date on the target device; repeat the process starting with agent sideloading
Not enough disk space or FAT32-formatted external drive
You need enough free disk space to fit the file system image. If using an external drive, make sure to format it in a file system other than FAT32, which limits file sizes to 4GB.
The extraction agent is not running or running in background
Ensure that the extraction agent runs as a foreground app during the entire extraction.
Wireless networks not fully disabled
First and foremost, the device must be placed into airplane mode during the extraction. However, depending on the last settings, the Wi-Fi and Bluetooth toggles may not be automatically disabled when the device enters airplane mode.
Solution: place the device into airplane mode first, then check and manually disable the Wi-Fi and Bluetooth toggles.
Error: “All exploits failed”
Cause: too long or too short a delay after booting or restarting the device.
Explanation: the exploits used by the extraction agent are time-sensitive. Some iOS versions require a delay of no more than 10 seconds after a reboot before launching the extraction agent, while iOS 16 requires a delay of approximately one minute to allow all kernel-level processes to stabilize. Providing an exact waiting time for each iOS version is challenging, so if you encounter issues with the exploit, try both shorter and longer delays, rebooting the device between attempts. In some cases, you may need to try up to five times.
Note: if the device has been running for a very long time (e.g. while sitting on a charger), the exploit will almost certainly fail. In this case, you will need to reboot the device.
Solution: reboot the device, wait 10 seconds to 1 minute.
Troubleshooting Guide
If none of the above resolves the issue, try identifying the issue by following steps from the Troubleshooting Guide.
Important: for the troubleshooting guide, always use a designated test device! Do not perform troubleshooting steps using the target device unless specifically instructed.
Step 1: Ensure Internet Connectivity on the Test Device
Ensure that the Internet sharing is working properly by checking that the Internet is accessible on the test device while wireless network interfaces (such as WiFi and mobile data) are disabled, and the text device is connect to your Mac computer via a cable. If you encounter issues with Internet sharing, refer to the “Misconfigured Internet Sharing for USB devices” section for solutions.
Step 2: Try Sideloading and Signing the Extraction Agent Without a Firewall
- Try signing the agent on the test device without running the firewall script. If successful, the issue may be related to firewall settings.
- If the agent signing fails even without a firewall, consider creating a new disposable Apple ID. Your goal is reaching a point where the entire process works correctly on the test device at this stage. If the agent signing still fails with a fresh Apple ID, contact our support team. You may need to update iOS Forensic Toolkit to the latest version.
Step 3: Try Sideloading and Signing the Extraction Agent With a Firewall
- Try sideloading and signing the extraction agent with the firewall script running.
- If the agent signing fails with the firewall script running, the issue is likely related to firewall settings. Occasionally, rebooting the test device while keeping the firewall script running may help resolve the issue. If rebooting doesn’t solve the problem, please contact our support team.
Step 4: Troubleshoot on the Target Device
If all previous steps were successful on the test device but signing the agent still fails on the target device, follow these steps:
- Disconnect the target device from the computer and reconnect it, then attempt to sign the agent again (ensure that the firewall script is running).
- If the issue persists, try disconnecting and rebooting the target device, and then reconnect it (with the firewall script running).
By following these steps, you should be able to troubleshoot and resolve common sideloading and signing issues. If you encounter any persistent problems, do not hesitate to contact our support team for further assistance.