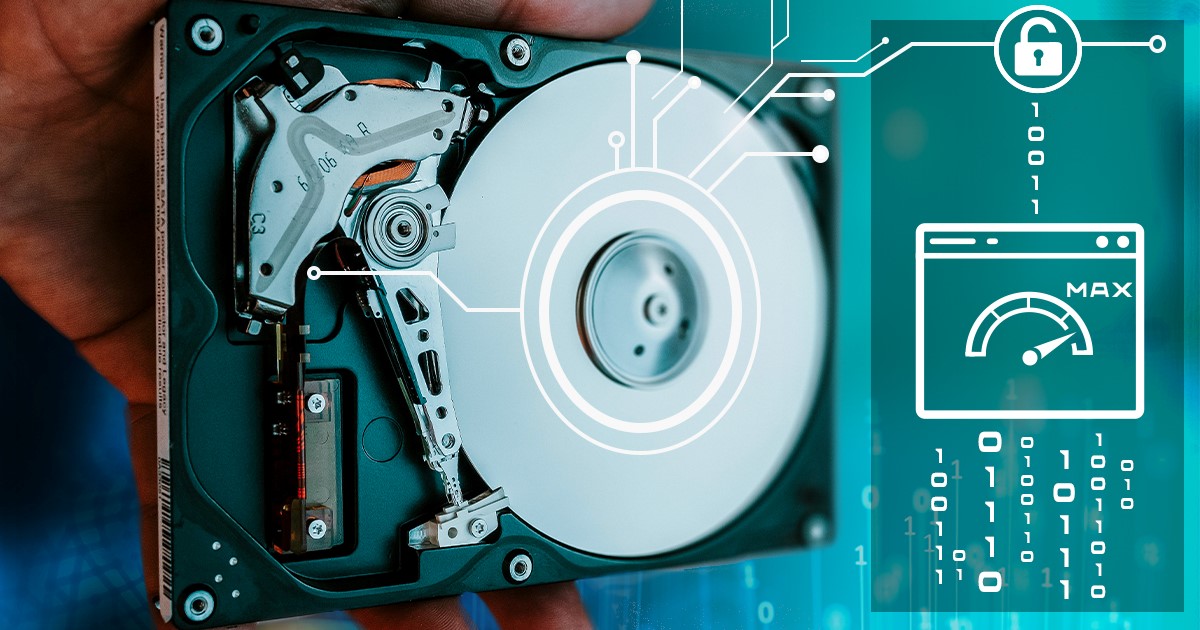
The past two years have become a turning point in iOS acquisition. The release of a bootrom-based exploit and the corresponding jailbreak made BFU acquisition possible on multiple devices regardless of security patches. Another exploit covers the entire iOS 13 range on all devices regardless of their hardware revision. ElcomSoft developed a jailbreak-free extraction method for the entire iOS 9.0-13.7 range. Let’s see what low-level acquisition options are available today, and when to use what.
After adding jailbreak-free extraction for iOS 13.5.1 through 13.7, we now support every Apple device running any version of iOS from 9.0 through 13.7 with no gaps or exclusions. For the first time, full file system extraction and keychain decryption are possible on all devices running these iOS versions.
Elcomsoft Distributed Password Recovery and Hashcat support a number of different attacks ranging from brute-force all the way to scriptable, dictionary-based attacks. The costs and performance are extremely important factors. We charge several hundred dollars for what, in the end, can be done with a free tool. Which tool has better performance, and are the extra features worth the price premium? Let’s check it out.
When adding a new encryption format or comparing the performance of different password recovery tools, we routinely quote the recovery speed expressed in the number of passwords per second. But what is the true meaning of password recovery speeds? Do the speeds depend solely, or at all, on the encryption algorithm? What’s “military grade” encryption, and does it guarantee the security of your data? And why on Earth breaking AES-256 encryption takes so vastly different effort in different file formats? Read along to find out.
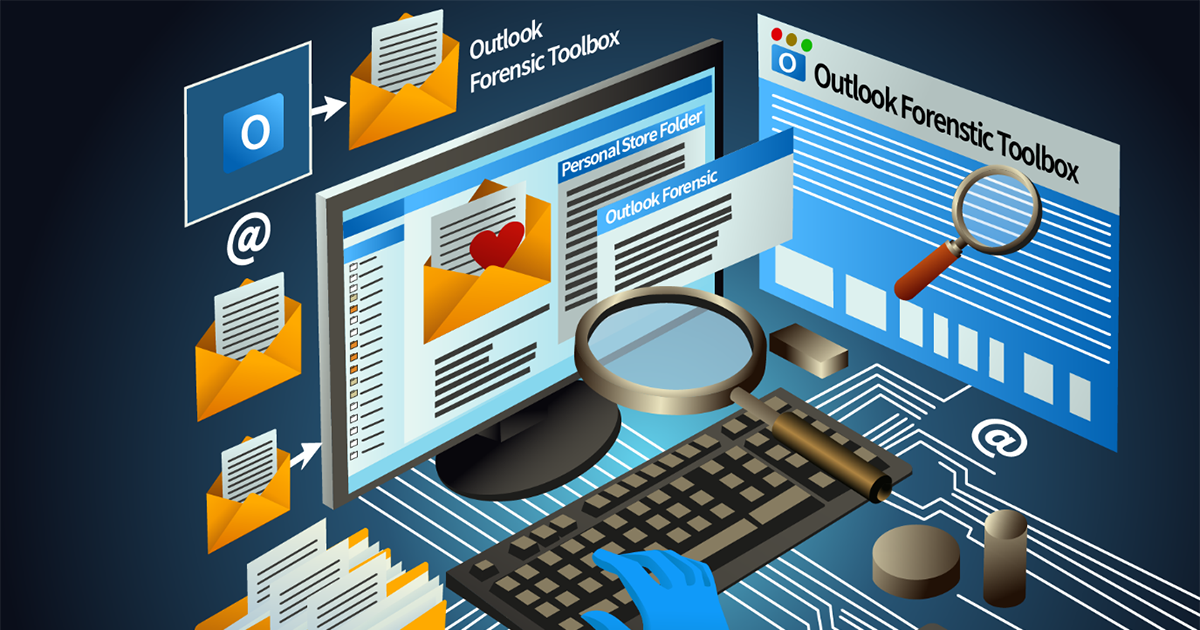
Accessing a locked system is always a challenge. Encrypted disks and encrypted virtual machines, encrypted files and passwords are just a few things to mention. In this article we are proposing a straightforward workflow for investigating computers in the field.
The user interface is a major advantage of Elcomsoft tools. Setting up attacks in Elcomsoft Distributed Password Recovery is simpler and more straightforward compared to the command-line tool. In this article, we’ll talk about the general workflow, the use and configuration of distributed and cloud attacks in both products.
After publishing the first article in the series, we received numerous comments challenging our claims. We carefully reviewed every comment, reread and reevaluated our original article. Elcomsoft vs. Hashcat Rev.1.1 is here.
If you are familiar with iOS acquisition methods, you know that the best results can be obtained with a full file system acquisition. However, extracting the file system may require jailbreaking, which may be risky and not always permitted. Are there any reasons to use jailbreaks for extracting evidence from Apple devices?
Hashcat is a great, free tool competing head to head with the tools we make. We charge several hundred dollars for what, in the end, can be done with a free tool. What are the reasons for our customers to choose ElcomSoft products instead of Hashcat, and is the expense justified? We did our best to compare the two tools to help you make the informed decision.
Four years ago, we published our first book: Mobile Forensics – Advanced Investigative Strategies. We are really proud of this achievement. Do you want to know the story behind it and what’s changed since then in mobile and cloud forensics? Here are some insides (but please do not tell anyone!)