- Home
- Categories
- Tags
-
Tips & Tricks
- More on Apple Developer Accounts
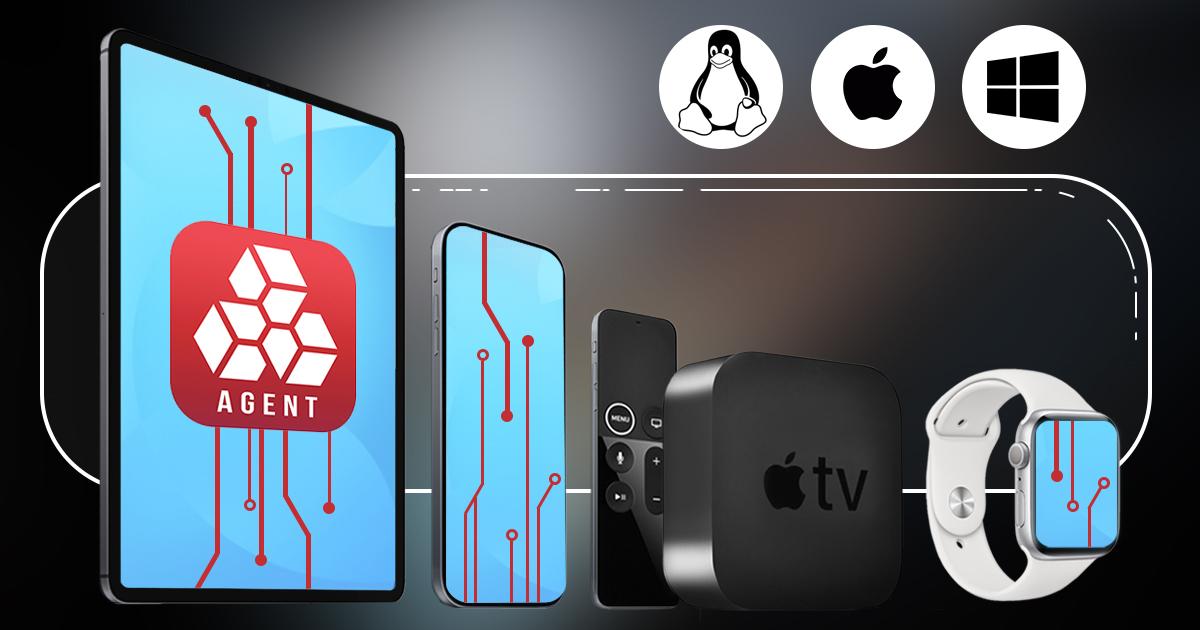
- iOS Forensic Toolkit: macOS, Windows, and Linux Editions Explained
- iCloud Extraction Turns Twelve
- Elcomsoft Forensic Acquisition System (EFAS)
- The Implications of Resetting the Screen Lock Passcode in iOS Forensics
- All You Wanted To Know About iOS Backups
- Resource Management in Distributed Password Attacks
- Bootloader-Level Extraction for Apple Hardware
- Navigating NVIDIA's Super 40-Series GPU Update: A Guide for IT Professionals
- When Extraction Meets Analysis: Cellebrite Physical Analyzer
- More...
- Events