Conferences are good. When attending Mobile Forensics Conference this year (and demoing our iOS Forensic Toolkit), we received a lot of requests for tools aimed at BlackBerry forensics. Sorry guys, we can’t offer the solution for physical acquisition of BlackBerries (yet), but there is something new we can offer right now.
 RIM BlackBerry smartphones have been deemed the most secure smartphones on the market for a long, long time. They indeed are quite secure devices, especially when it comes to extracting information from the device you have physical access to (i.e. mobile phone forensics). It is unfortunate, however, that a great deal of that acclaimed security is achieved by “security through obscurity”, i.e. by not disclosing in-depth technical information on security mechanisms and/or their implementation. The idea is to make it more difficult for third parties to analyze. Some of us here at Elcomsoft are BlackBerry owners ourselves, and we are not quite comfortable with unsubstantiated statements about our devices’ security and blurry “technical” documentation provided by RIM. So we dig.
RIM BlackBerry smartphones have been deemed the most secure smartphones on the market for a long, long time. They indeed are quite secure devices, especially when it comes to extracting information from the device you have physical access to (i.e. mobile phone forensics). It is unfortunate, however, that a great deal of that acclaimed security is achieved by “security through obscurity”, i.e. by not disclosing in-depth technical information on security mechanisms and/or their implementation. The idea is to make it more difficult for third parties to analyze. Some of us here at Elcomsoft are BlackBerry owners ourselves, and we are not quite comfortable with unsubstantiated statements about our devices’ security and blurry “technical” documentation provided by RIM. So we dig.
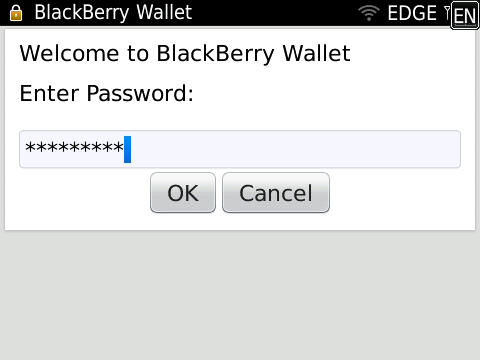
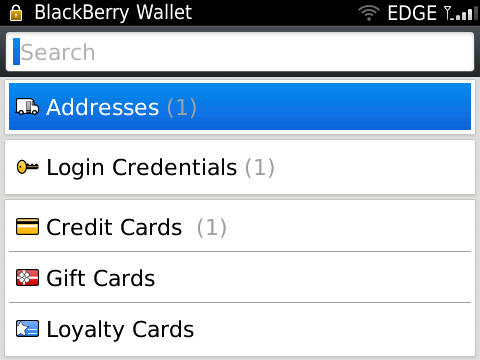
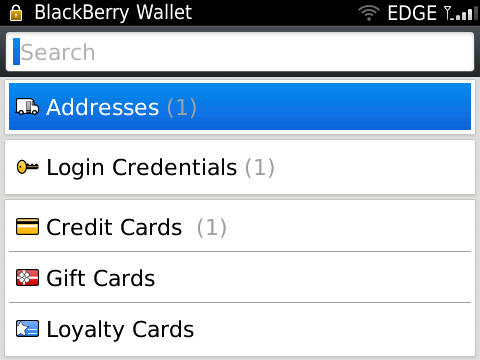
Our first two targets are the apps providing secure storage of sensitive data: BlackBerry Password Keeper and BlackBerry Wallet. These applications are provided by RIM for free; Password Keeper is even included with each installation of BlackBerry OS. The two apps are the recommended way to store login credentials and other sensitive data such as credit card numbers. The data stored in those two apps could also be a wealth of information for investigators. According to RIM, all data is securely encrypted with AES-256. The encryption key is derived from user-specified master password, which can be different from device password. Password Keeper and Wallet master passwords can also be different.
Another notable fact is that Password Keeper and Wallet databases are included in the backup produced by BlackBerry Desktop Software. This means that, as a mobile forensics investigator, you can access those databases (containing encrypted data at this point) by either connecting suspects’ handset and running Desktop Software (if there is no password protection on the device) or by looking for stored device backups on suspects’ computer(s). And even if the backup you’ve been able to get a hold of is encrypted, our Elcomsoft Phone Password Breaker can recover the password for it .
Once you’ve got the (unencrypted) backup, Password Keeper and Wallet databases are accessible. The problem is that their data are still encrypted. And this is exactly what today’s EPPB release is about: recovering master passwords for Password Keeper and Wallet databases. Now you can load a BlackBerry device backup into EPPB and run password recovery against Password Keeper and Wallet databases. And what’s really good about this is that password recovery rate is great – hundreds of thousands and up to several millions passwords per second on modern CPU, depending on BlackBerry OS version. To the best of our knowledge, there were no tools capable of doing this until now, so we're proud to be the world’s first again, offering our customers unique functionality that’s not available in other vendors’ products.
So, you were able to discover the master password, what's next? Right now you have two options:
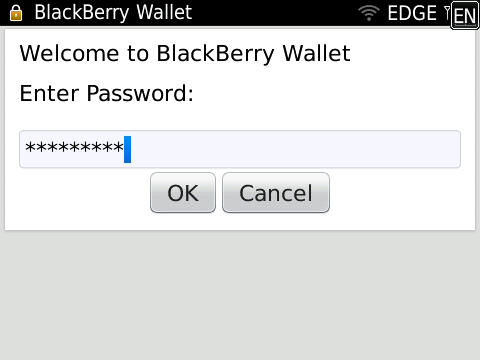
- Use BlackBerry Simulator, restore the backup to it, and use the recovered master password(s) to enter Password Keeper and/or Wallet. Access stored data as usual.
- Use Elcomsoft BlackBerry Backup Explorer, which can now show Password Keeper and Wallet data (as of version 9.61 being released today).
The third option to view Password Keeper and Wallet data within EPPB itself will be probably added with the next update. Speaking of updates, I'd like to tell you that this BlackBerry-related addition is really small compared to what's in the queue. If things go well, we hope to release "the next big thing" within 1-1.5 months from now. You're going to love it, I promise :-).
P.S. For those technically inclined out there, here’s a brief summary:
BlackBerry Password Keeper database format and protection is the same for OS 5, OS 6, and OS7. Per-item encryption key is derived by computing 3 (three) iterations of PBKDF2-SHA1 with master password and per-item salt.
Wallet database format and protection differs between OS 5 and OS 6/7.
For Wallet in OS 5, per-item encryption key is derived by computing 3 (three) iterations of PBKDF2-SHA1 with SHA-256 hash of master password and per-item salt.
For Wallet in OS 6 and OS 7, per-item encryption key is derived by computing a random number of iterations (between 50 and 100) of PBKDF2-SHA1 with SHA-512 hash of master password and per-item salt.
Encryption in all above formats is AES-256 in ECB (!) mode, SHA-1 hash of the data is appended before encrypting; data is padded as per PKCS #5.
In my opinion, should RIM have opted to be more open about their security mechanisms, someone (maybe even someone from their own team) could possibly point out that the level of protection against password recovery attacks is not sufficient for 2011.