iOS 16 brings many changes to mobile forensics. Users receive additional tools to control the sharing and protection of their personal information, while forensic experts will face tighter security measures. In this review, we’ll talk about the things in iOS 16 that are likely to affect the forensic workflow.
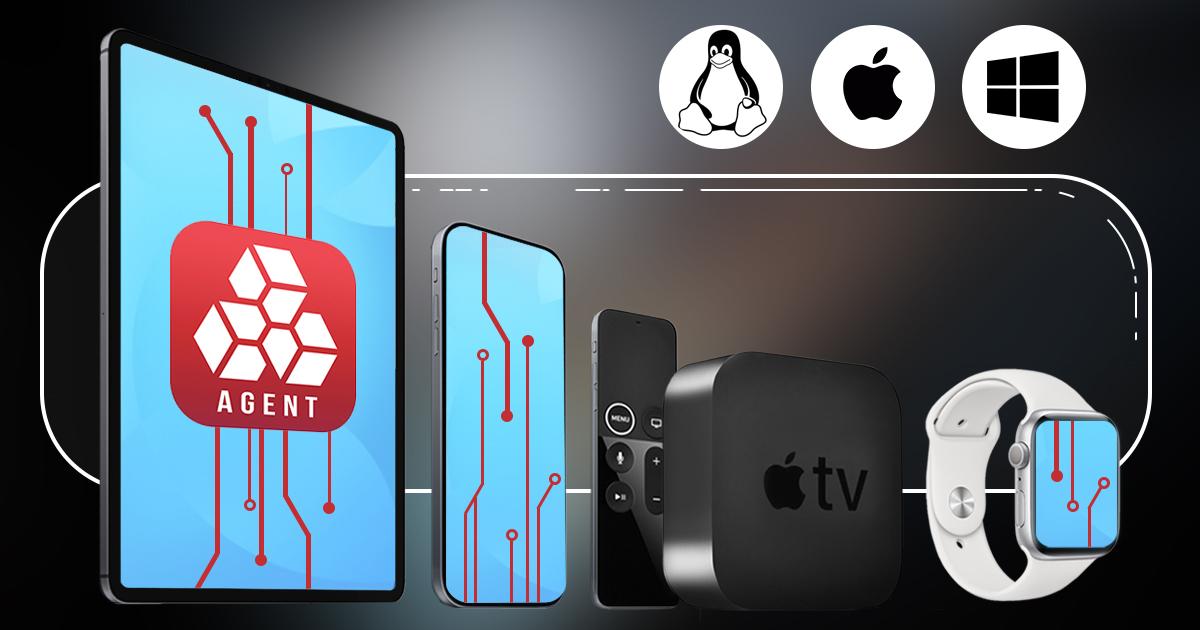
iOS Forensic Toolkit 8.0 is officially released! Delivering forensically sound checkm8 extraction and a new command-line driven user experience, the new release becomes the most sophisticated mobile forensic tool we’ve released to date.
Bootloader-based acquisition is the only 100% forensically sound data extraction method for Apple devices. It is the only way to acquire the full set of data from those devices that run iOS 16, albeit with a huge caveat that makes the whole thing more of a brain exercise than a practical forensic tool. Let’s review the iOS 16 compatibility in iOS Forensic Toolkit and go through the whole process step by step.
DFU (Device Firmware Update) is a special service mode available in many Apple devices for recovering corrupted devices by uploading a clean copy of the firmware. Forensic specialists use DFU during checkm8 extractions (Elcomsoft iOS Forensic Toolkit). Unlike Recovery, which serves a similar purpose, DFU operates on a lower level and is undocumented. Surprisingly, there might be more than one DFU mode, one being more reliable than the others when it comes to forensic extractions. The method described in this article works for the iPhone 8, 8 Plus and iPhone X.