June 14th, 2018 by Vladimir Katalov
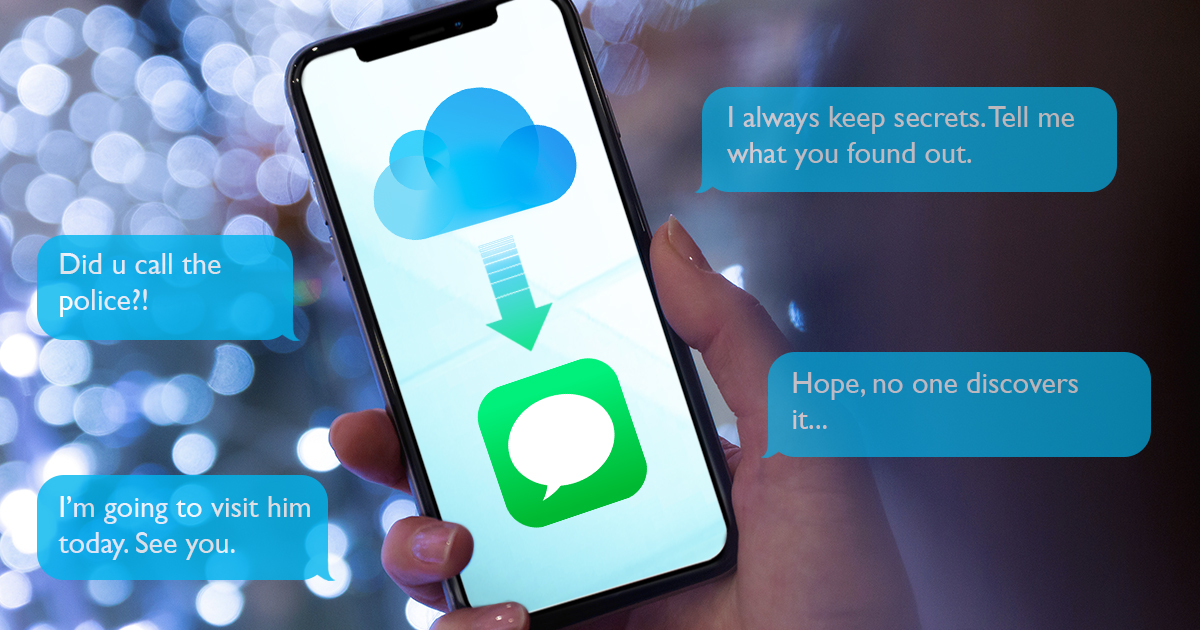
We also trust these companies in ways that we do not understand yet. How many of you trust Apple? No voting… Just me 🙂 Damn! OK. May I ask you a very good question. Trusting to do what? Trusting when they say: “iMessages are end-to-end encrypted”? I mean, with all of that massive security engineering, to make sure it’s as good as it can be, so they genuinely believe they’ve done that. I do, generally, they’re great people. But… people believe themselves they can defend themselves against the Russians. If the Russians specifically targeted Apple, it’s only they can defend themselves. – Ian Levy, director at the GCHQ on anniversary of the foundation of the FIPR event that was held on 29/04/2018).
Read the rest of this entry »