November 30th, 2023 by Oleg Afonin
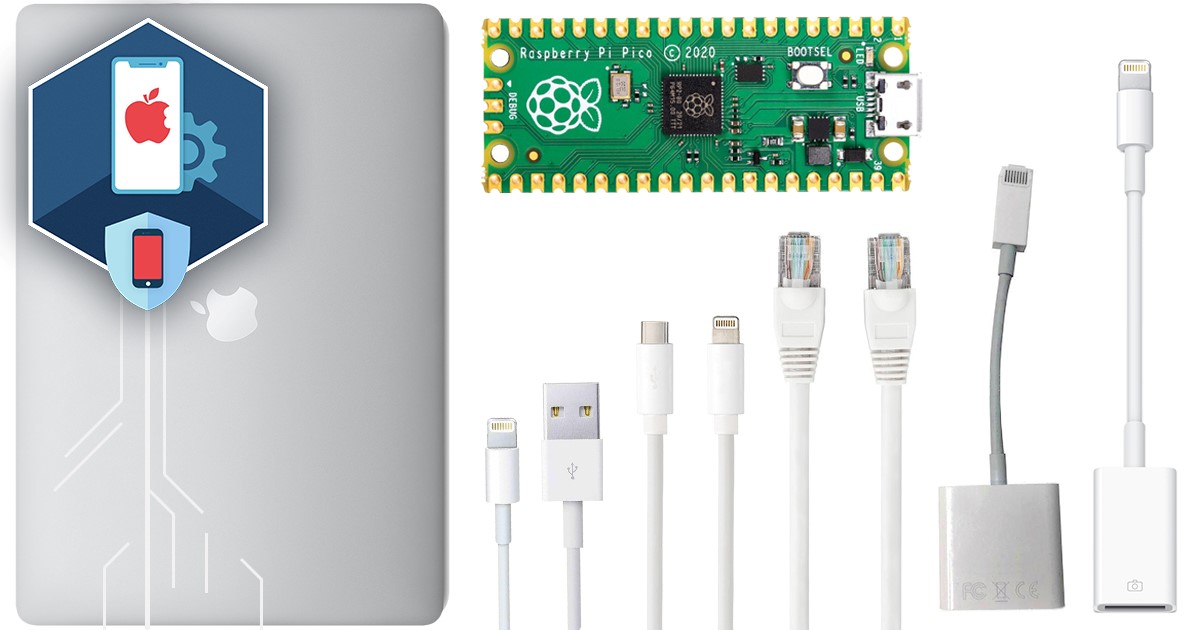
The latest update to the iOS Forensic Toolkit has expanded data extraction support for older models of Apple Watch, introducing low-level extraction capabilities for Apple Watch Series 0, Series 1, and Series 2. In a landscape where new devices are released on a yearly schedule, we stand committed to a balanced approach. While it’s easy for many to dismiss older devices, we recognize their significance as they frequently reappear in the labs of forensic experts. It is important to emphasize that, unlike many, we cater to the needs of experts who have to deal with legacy devices. This enhancement enables macOS and Linux users to delve deeper into these watches, retrieving crucial information such as passwords and complete file systems.
Read the rest of this entry »