- Home
- Categories
- Tags
-
Tips & Tricks
- Using the Extraction Agent in 2026: Compatibility, Signing, Firewall, and Extraction Tips
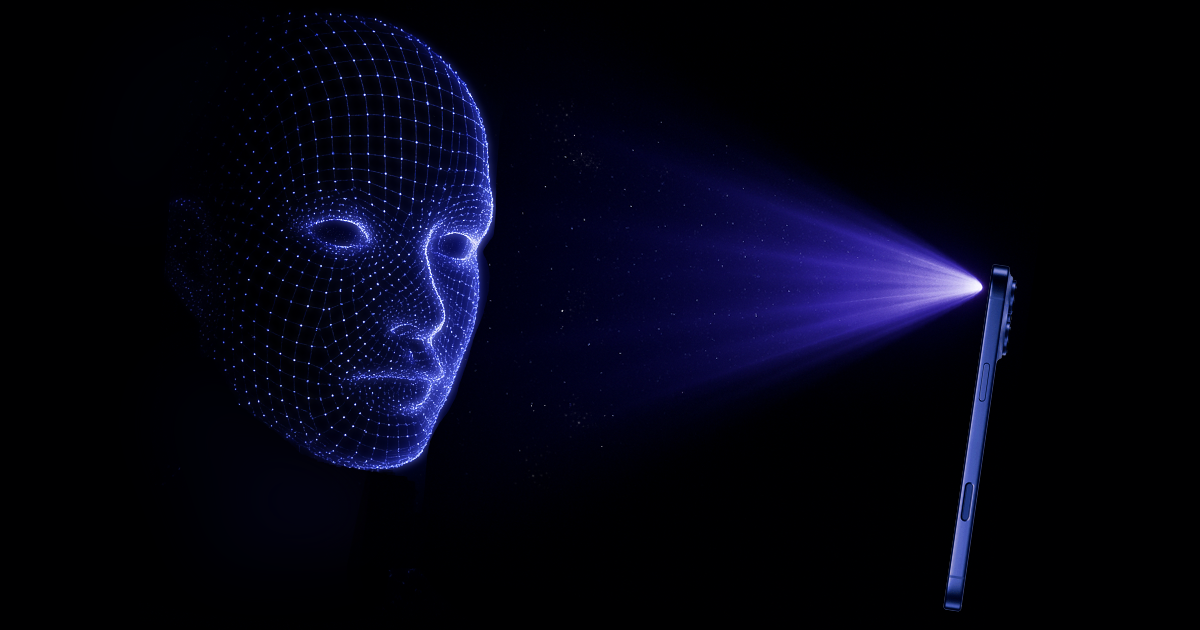
- Low-Level Extraction for iOS 17 and 18
- Perfect Acquisition: The True Physical Acquisition
- Perfect Acquisition With Passcode Unlock for A8/A8X Devices
- Introducing Elcomsoft Quick Triage
- Breaking Barriers: First Full File System Extraction from Apple TV 4K Running tvOS 26
- Which Versions of iOS Are Supported, and Why "It Depends" Is The Best Answer
- Don’t Be a Louvre: How Weak Passwords and Unpatched Software Encourage Breaches
- Exploring iPadOS, tvOS and audioOS 17 and 18 Devices: File System and Keychain Extraction
- All USB Cables Are Equal, But Some Are More Equal Than Others
- More...
- Events