October 15th, 2024 by Vladimir Katalov
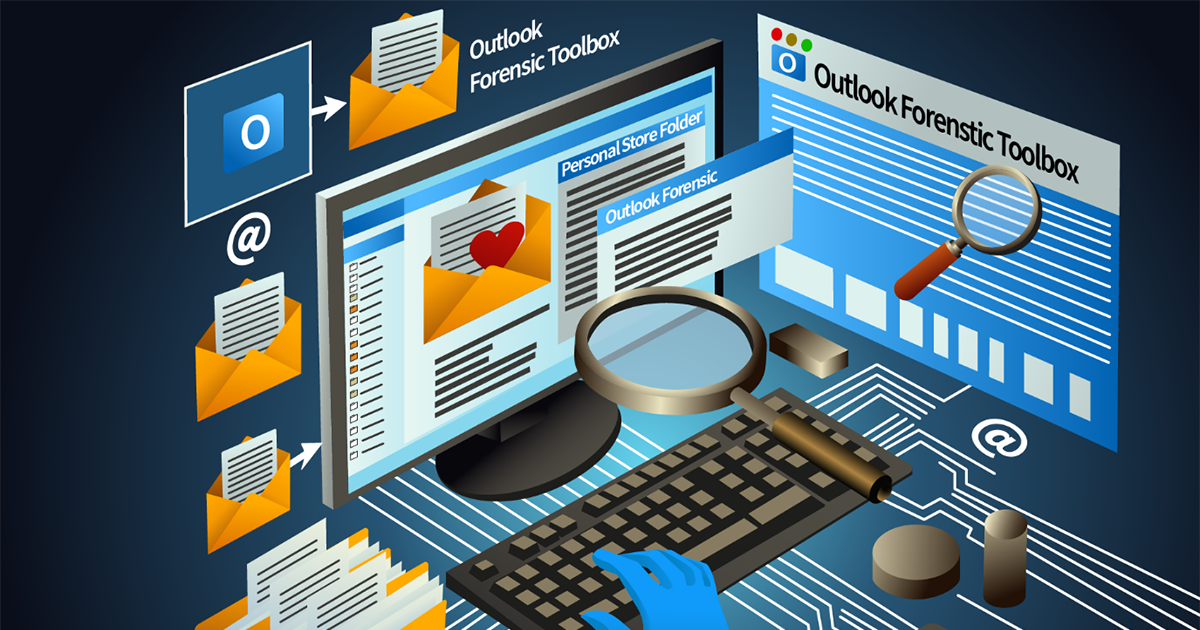
What can a forensic expert find in an Outlook data file? Can they recover deleted emails, contacts and appointments from Microsoft Outlook? Can users erase unwanted correspondence from Outlook? In this article, we’ll demonstrate how experts can recover valuable information from Outlook data files (PST/OST), including deleted emails, contacts, attachments, and appointments. Even when users attempt to erase unwanted correspondence, traces often remain within the database. With the right tools, experts can extract and analyze this hidden data to uncover critical evidence.
Read the rest of this entry »